How hackers use idle scans in port scan attacks
Por um escritor misterioso
Last updated 31 março 2025
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.

Port Scanning - an overview
PPT - Port Scanning PowerPoint Presentation, free download - ID:4633948
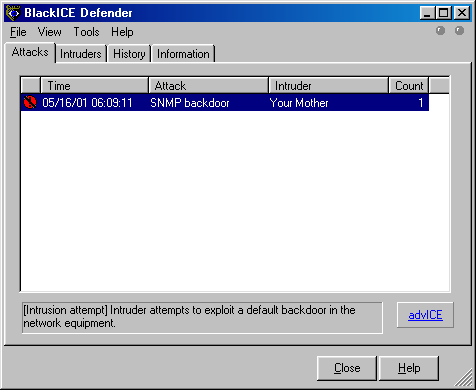
Subverting Intrusion Detection Systems

NMAP by Shrikant Antre & Shobhit Gautam
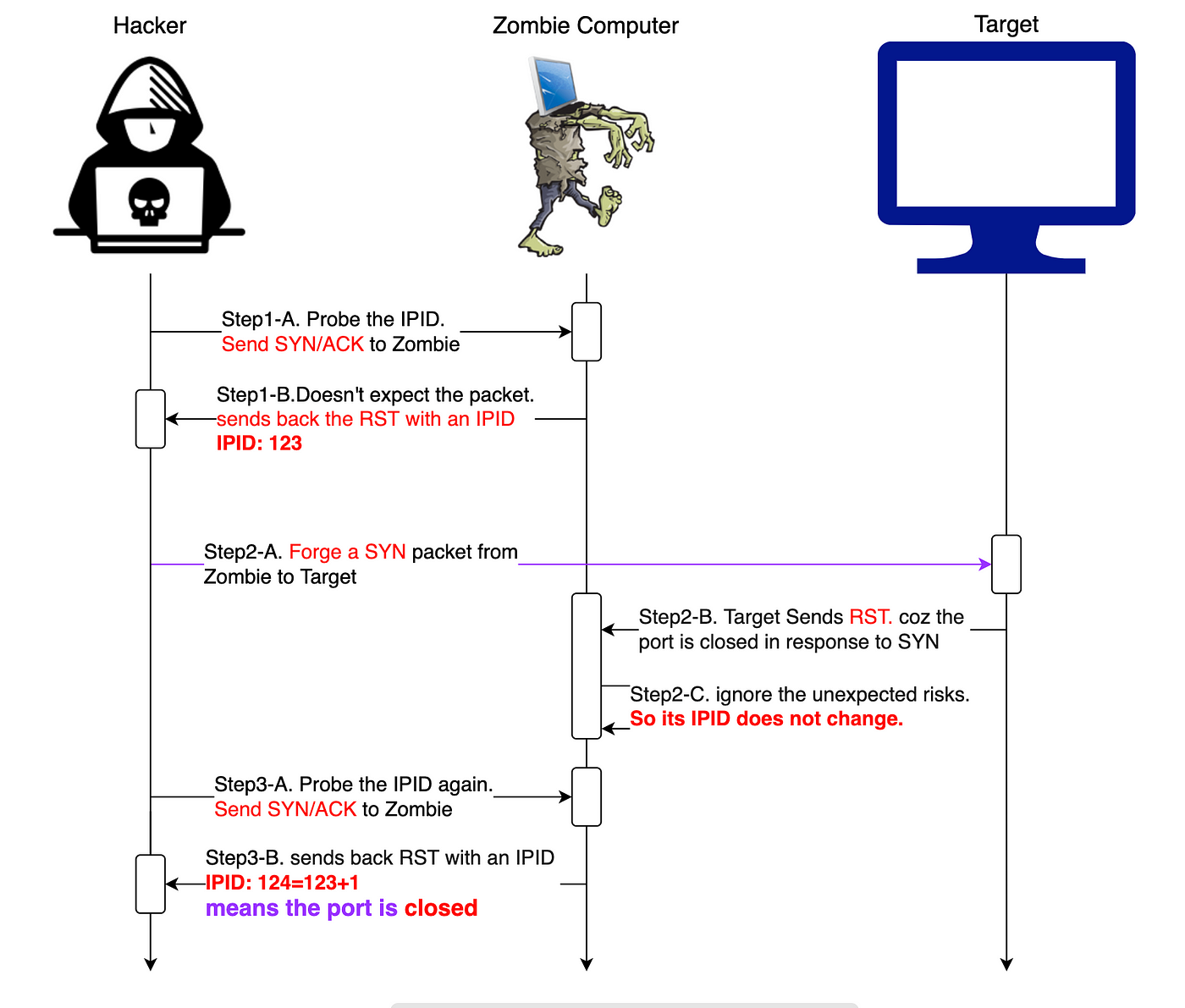
Nmap cheat sheet: From discovery to exploits, part 2: Advance port scanning with Nmap and custom idle scan

How to hide yourself using Idle scan (-sl) - Port scanning tutorial

Nmap cheat sheet: From discovery to exploits, part 2: Advance port scanning with Nmap and custom idle scan
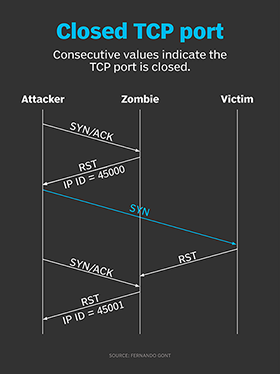
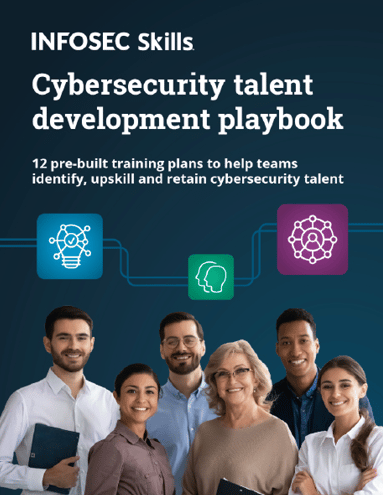
Zombie/Idle scan working principle, by NGU
How hackers use idle scans in port scan attacks
What Is Nmap? A Comprehensive Tutorial For Network Mapping

Port Scanning Tutorial for Hackers - Basics
Recomendado para você
-
 IP Chicken - What is my IP address Free public IP lookup31 março 2025
IP Chicken - What is my IP address Free public IP lookup31 março 2025 -
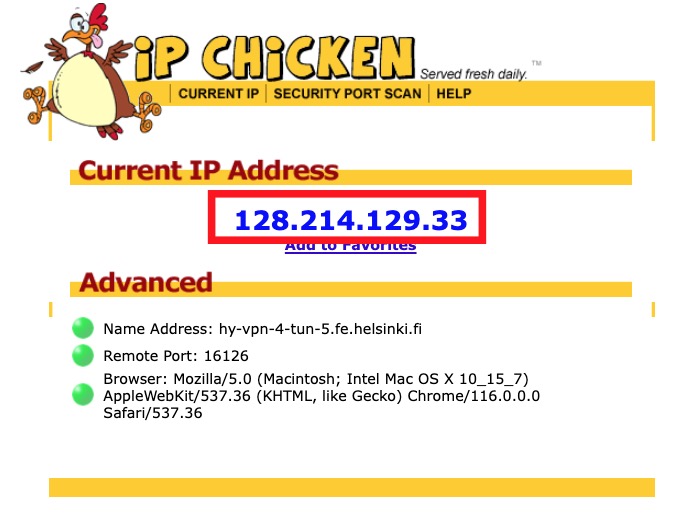 HY-VPN – Checking functionality and errors (Linux)31 março 2025
HY-VPN – Checking functionality and errors (Linux)31 março 2025 -
 Brisson teaches internet safety - Munising Beacon31 março 2025
Brisson teaches internet safety - Munising Beacon31 março 2025 -
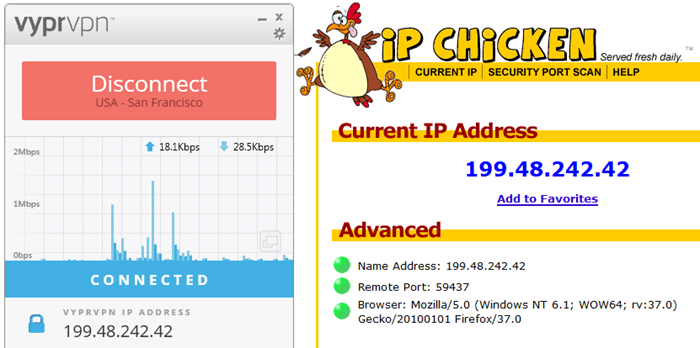 VyprVPN Review - Secure Personal VPN Service Review31 março 2025
VyprVPN Review - Secure Personal VPN Service Review31 março 2025 -
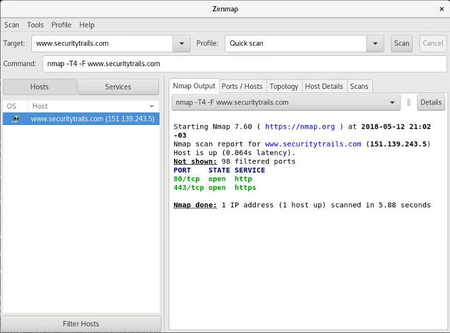 Top 5 Most Popular Port Scanners in CyberSecurity31 março 2025
Top 5 Most Popular Port Scanners in CyberSecurity31 março 2025 -
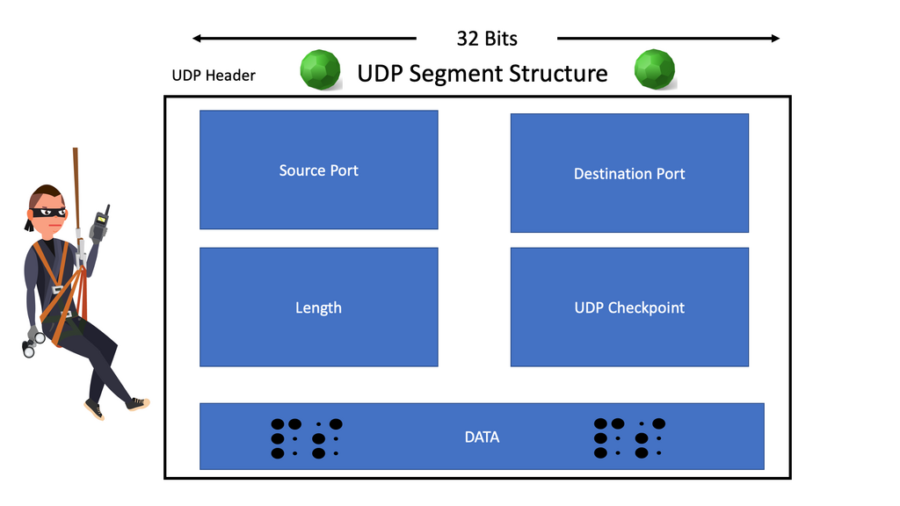 UDP Scan31 março 2025
UDP Scan31 março 2025 -
 LC EP1: TP Link ER-605/ER-7206 , OC-200, SG-2210P, EAP-235 Omada & SDN Out-of-Box Experience31 março 2025
LC EP1: TP Link ER-605/ER-7206 , OC-200, SG-2210P, EAP-235 Omada & SDN Out-of-Box Experience31 março 2025 -
Ethical Hacking With Net31 março 2025
-
 Port Scanning Techniques: An Introduction31 março 2025
Port Scanning Techniques: An Introduction31 março 2025 -
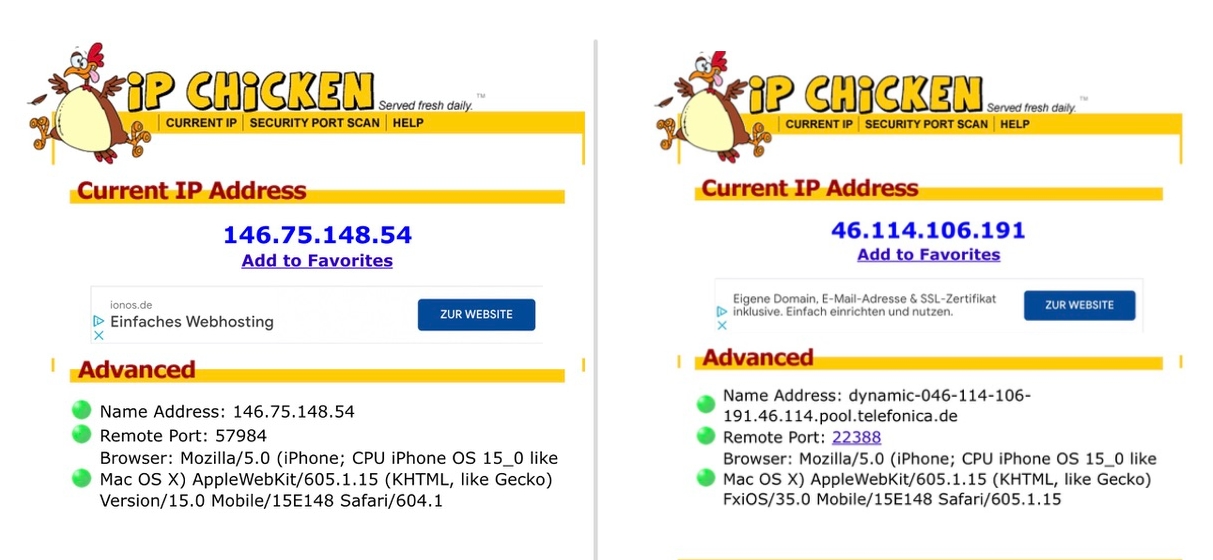 iOS 15: Hide IP address in Safari31 março 2025
iOS 15: Hide IP address in Safari31 março 2025
você pode gostar
-
 Jogo de tabuleiro variado para crianças no Shoptime31 março 2025
Jogo de tabuleiro variado para crianças no Shoptime31 março 2025 -
 World's 50 Most Valuable Soccer Teams: Man United, Real Madrid Lead –31 março 2025
World's 50 Most Valuable Soccer Teams: Man United, Real Madrid Lead –31 março 2025 -
 Fruit Script Blox Fruit Photos, Download The BEST Free Fruit31 março 2025
Fruit Script Blox Fruit Photos, Download The BEST Free Fruit31 março 2025 -
Realm of Darkness: Kino no Tabi - The Beautiful World31 março 2025
-
Steam Workshop::Bioshock Infinite Menu BG31 março 2025
-
 tori vega - Google Search Mujeres, Hermosas celebridades, Celebridades31 março 2025
tori vega - Google Search Mujeres, Hermosas celebridades, Celebridades31 março 2025 -
 Standalone VR: What You Need to Know About All-in-One Headsets31 março 2025
Standalone VR: What You Need to Know About All-in-One Headsets31 março 2025 -
 hisoka e uns dos meus : r/HUEstation31 março 2025
hisoka e uns dos meus : r/HUEstation31 março 2025 -
 Kusuriya no Hitorigoto? (Anime, Serie, finden)31 março 2025
Kusuriya no Hitorigoto? (Anime, Serie, finden)31 março 2025 -
 Foundational Jump Development for All Levels31 março 2025
Foundational Jump Development for All Levels31 março 2025