SILKLOADER: How Hackers Evade Detection
Por um escritor misterioso
Last updated 02 abril 2025

As the cyber threat landscape continues to evolve, hackers are employing increasingly sophisticated techniques to evade detection. One such example is the SILKLOADER malware, which has recently gained attention for its stealth capabilities.
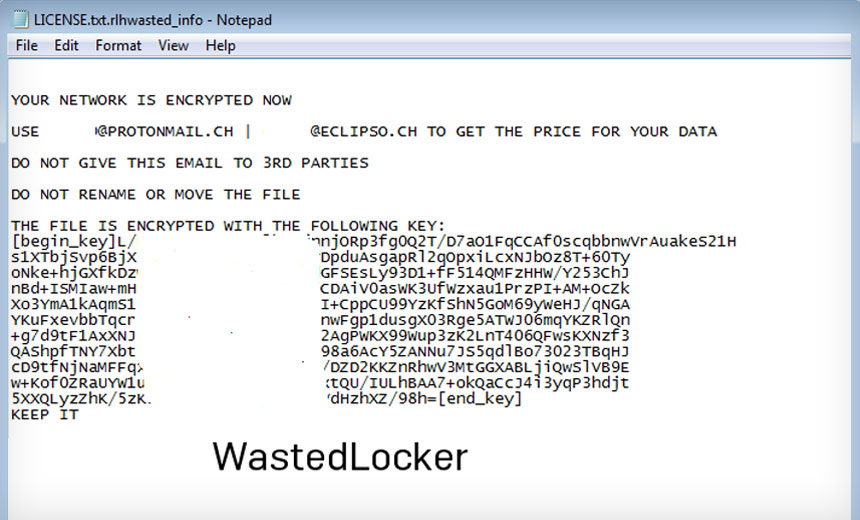
How WastedLocker Evades Anti-Ransomware Tools

Chinese Silkloader cyber attack tool falls into Russian hands
Risky Biz News: Google wants to reduce lifespan of TLS certificates from one year to just 90 days

Evading AV Software « Null Byte :: WonderHowTo

1-15 March 2023 Cyber Attacks Timeline – HACKMAGEDDON
Windows Red Team Defense Evasion Techniques - HackerSploit Blog

How Hackers Are “Blending In” to Evade Detection

MALWARE DETECTION : EVASION TECHNIQUES - CYFIRMA

Lynx-CERT

Cl0p hits Hitachi Energy. TikTok surveillance investigated. BreachForums arrest. Hacktivists, torrents in the hybrid war.
Recomendado para você
-
 Evade (Roblox) Know Your Meme02 abril 2025
Evade (Roblox) Know Your Meme02 abril 2025 -
 EVADE (BEST) – ScriptPastebin02 abril 2025
EVADE (BEST) – ScriptPastebin02 abril 2025 -
 Evade Script/GUI Review02 abril 2025
Evade Script/GUI Review02 abril 2025 -
 New Script: 💠 Roblox Evade Script : r/Zaptosis02 abril 2025
New Script: 💠 Roblox Evade Script : r/Zaptosis02 abril 2025 -
 Evade Script Pastebin - Anti Next Bot, ESP & More02 abril 2025
Evade Script Pastebin - Anti Next Bot, ESP & More02 abril 2025 -
 2 Late 2 Evade by Script Idea02 abril 2025
2 Late 2 Evade by Script Idea02 abril 2025 -
 David J. Ferreira on 'Evade'02 abril 2025
David J. Ferreira on 'Evade'02 abril 2025 -
 Evade News on X: If You Want To Support Oster And Beef You Can02 abril 2025
Evade News on X: If You Want To Support Oster And Beef You Can02 abril 2025 -
 How could I make a movement system like Evade - Scripting Support02 abril 2025
How could I make a movement system like Evade - Scripting Support02 abril 2025 -
Sophos - NEW from SophosLabs: AMSI bypasses remain tricks of the02 abril 2025
você pode gostar
-
 Epic Games' CEO blames Fortnite for the company's massive layoffs of almost 1000 workers - Meristation02 abril 2025
Epic Games' CEO blames Fortnite for the company's massive layoffs of almost 1000 workers - Meristation02 abril 2025 -
 Karts à venda UAI Fórmula Kart02 abril 2025
Karts à venda UAI Fórmula Kart02 abril 2025 -
 The Last of Us Series Creator Teases Joel's Fate in Season 202 abril 2025
The Last of Us Series Creator Teases Joel's Fate in Season 202 abril 2025 -
UFB 2 Fighting: Jogo de Luta – Apps no Google Play02 abril 2025
-
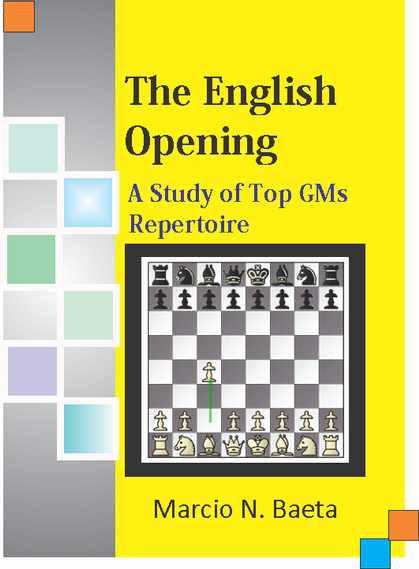 Abertura Inglesa - Advocacia, Pintura & Xadrez02 abril 2025
Abertura Inglesa - Advocacia, Pintura & Xadrez02 abril 2025 -
 THRONE AND LIBERTY REVELADA DATA DE LANÇAMENTO, GAMEPLAY E MUITO02 abril 2025
THRONE AND LIBERTY REVELADA DATA DE LANÇAMENTO, GAMEPLAY E MUITO02 abril 2025 -
Form Valkyrie Feathers Roblox Item - Rolimon's02 abril 2025
-
 FREE Info Session for Certification: Become a Resilience Toolkit Facilitator02 abril 2025
FREE Info Session for Certification: Become a Resilience Toolkit Facilitator02 abril 2025 -
 Clube Urca02 abril 2025
Clube Urca02 abril 2025 -
 How to Change Xbox Gamertag on Iphone?02 abril 2025
How to Change Xbox Gamertag on Iphone?02 abril 2025
