Malware analysis Malicious activity
Por um escritor misterioso
Last updated 02 abril 2025
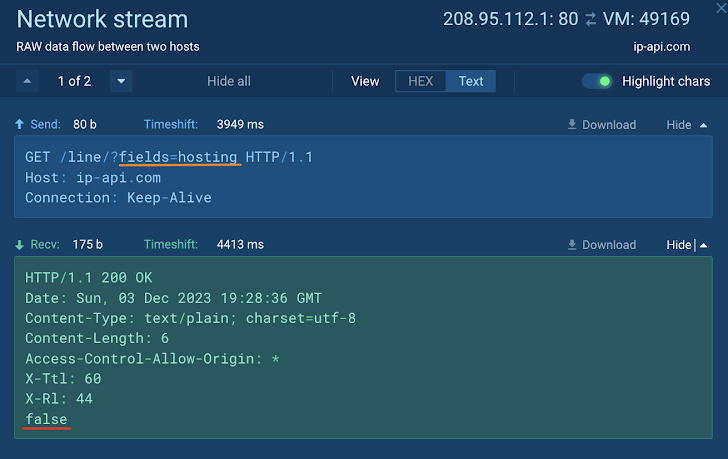
How to Analyze Malware's Network Traffic in A Sandbox

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Malware analysis metasploit.bat Malicious activity

How to build a malware analysis sandbox with Elastic Security

MetaDefender Cloud Advanced threat prevention and detection
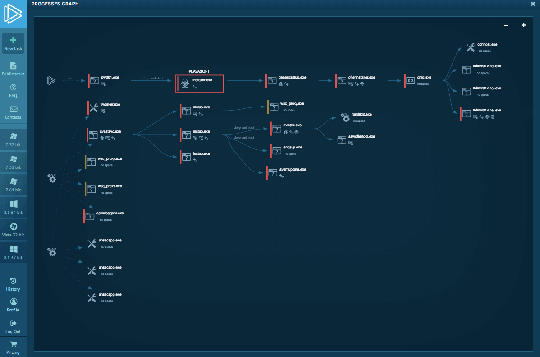
Interactive Online Malware Sandbox

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
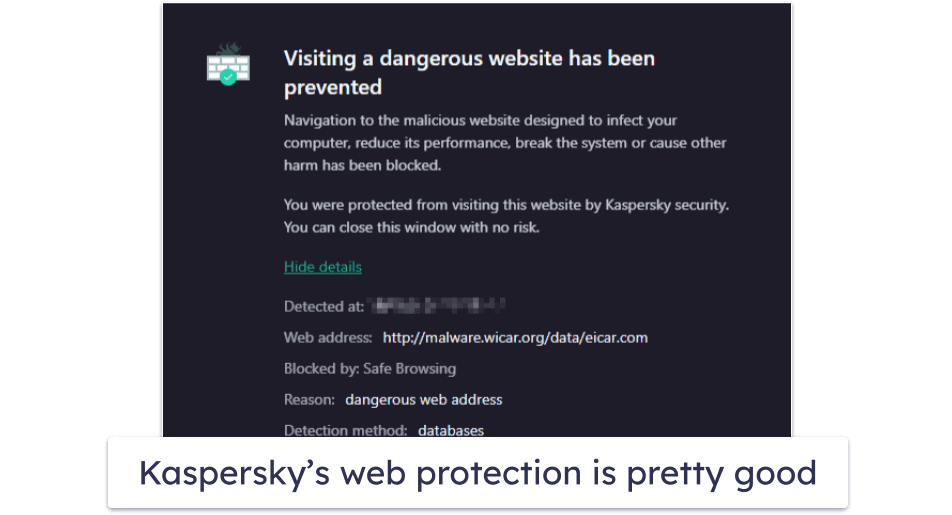
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
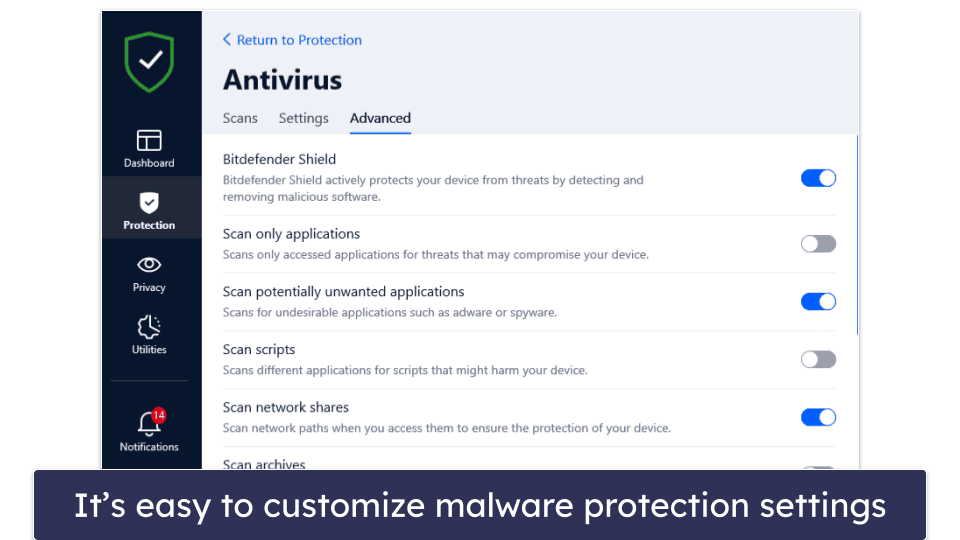
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

Malware analysis Program_Install_and_Uninstall Malicious activity
Recomendado para você
-
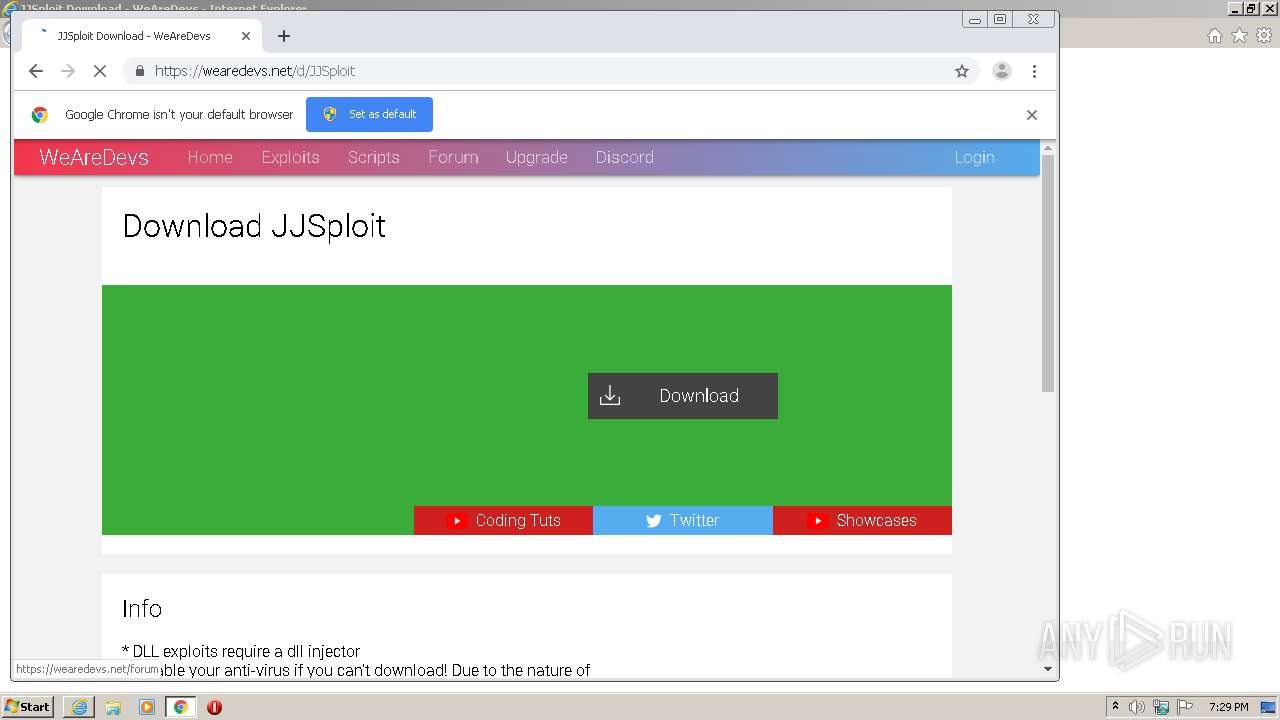
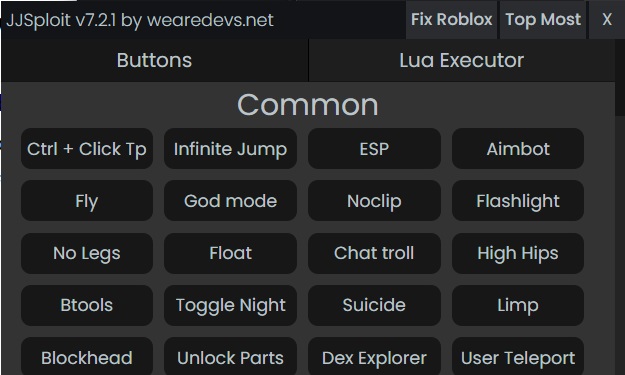 JJSploit for Roblox 7.2.1 Download For Windows PC - Softlay02 abril 2025
JJSploit for Roblox 7.2.1 Download For Windows PC - Softlay02 abril 2025 -
 Krnl Wearedevs GIF - Krnl Wearedevs Virus - Discover & Share GIFs02 abril 2025
Krnl Wearedevs GIF - Krnl Wearedevs Virus - Discover & Share GIFs02 abril 2025 -
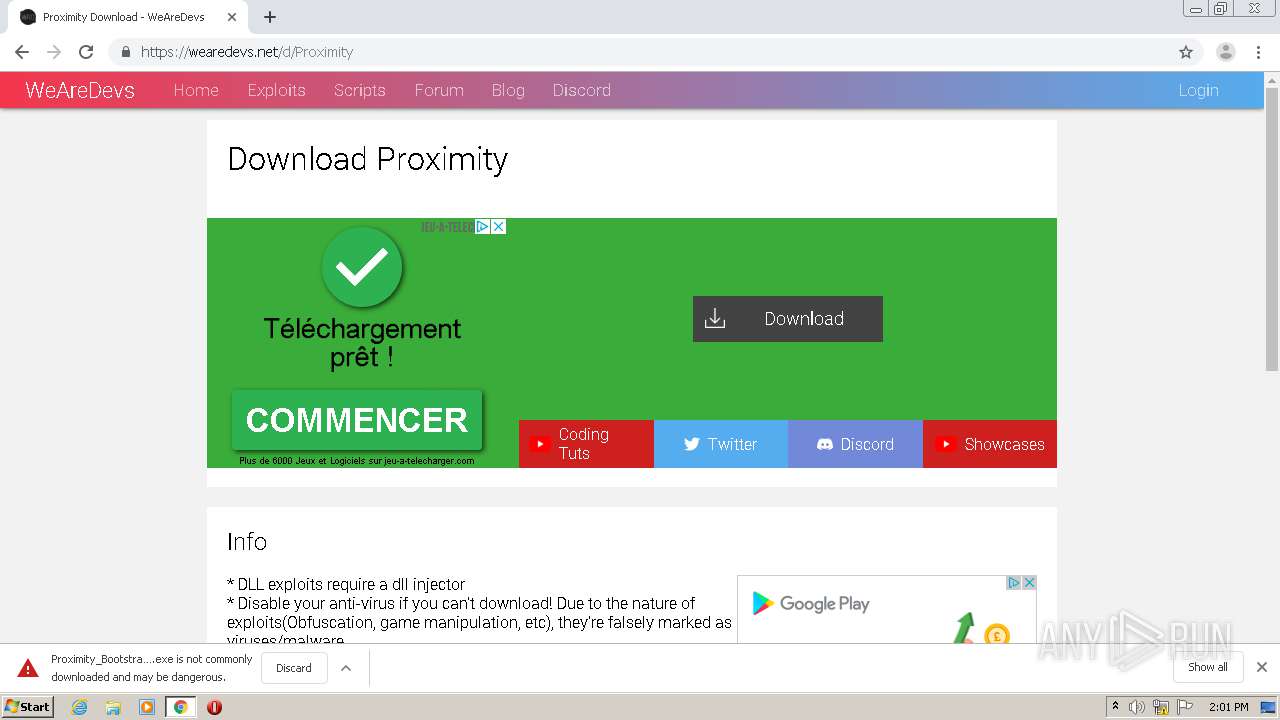 Malware analysis Malicious activity02 abril 2025
Malware analysis Malicious activity02 abril 2025 -
 Top 69 Similar websites like wearedevs.net and alternatives02 abril 2025
Top 69 Similar websites like wearedevs.net and alternatives02 abril 2025 -
 John Woods spoke at WeAreDevs Fintech today : r/AlgorandOfficial02 abril 2025
John Woods spoke at WeAreDevs Fintech today : r/AlgorandOfficial02 abril 2025 -
 Wearedevs.net é confiável? Wearedevs é segura?02 abril 2025
Wearedevs.net é confiável? Wearedevs é segura?02 abril 2025 -
WeAreDevs · GitHub02 abril 2025
-
 wearedevs – SlavConf02 abril 2025
wearedevs – SlavConf02 abril 2025 -
 Offical, Banshee Exploit, Full Lua Exploit02 abril 2025
Offical, Banshee Exploit, Full Lua Exploit02 abril 2025 -
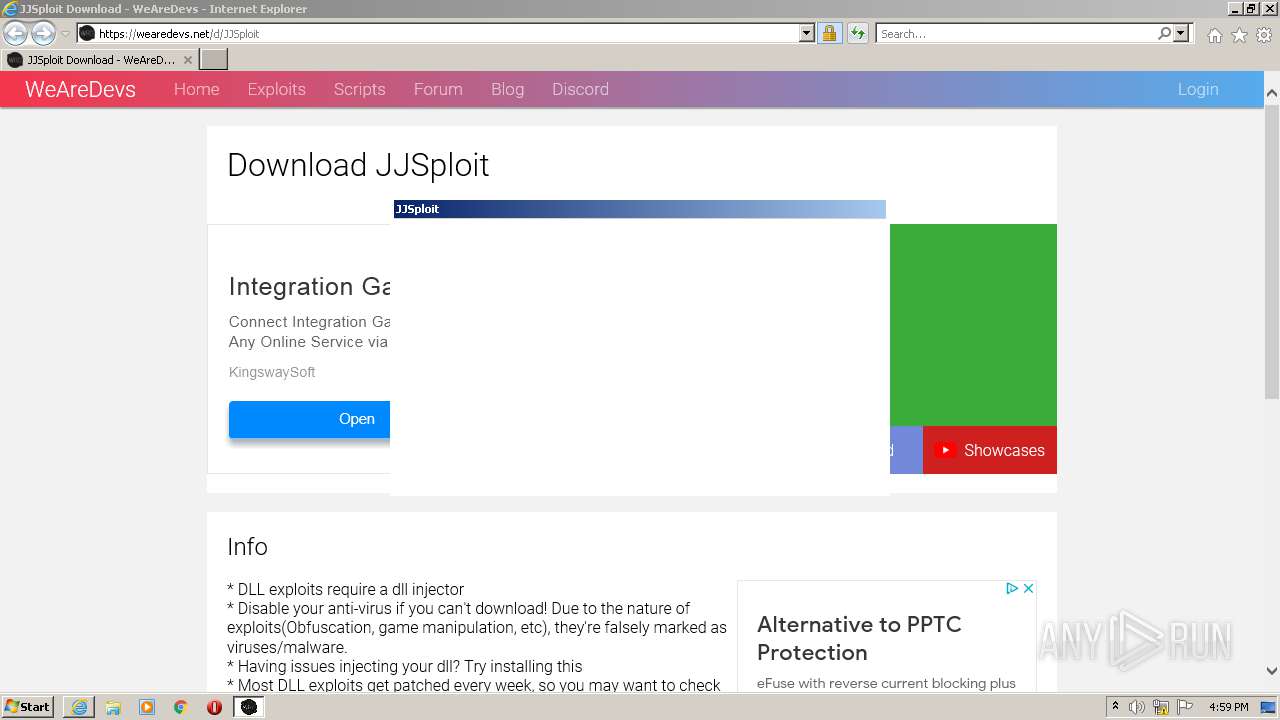 Malware analysis Malicious02 abril 2025
Malware analysis Malicious02 abril 2025
você pode gostar
-
 The Rock Reveals One Of His Biggest Regrets In Wrestling02 abril 2025
The Rock Reveals One Of His Biggest Regrets In Wrestling02 abril 2025 -
 Highway-Rail Grade Crossings Overview02 abril 2025
Highway-Rail Grade Crossings Overview02 abril 2025 -
 War Idea By Just_Limed : r/SlapBattles02 abril 2025
War Idea By Just_Limed : r/SlapBattles02 abril 2025 -
enviei errado entes mas ideias para gacha life02 abril 2025
-
 Tokyo Revengers Estreia da 2ª temporada ganha imagens02 abril 2025
Tokyo Revengers Estreia da 2ª temporada ganha imagens02 abril 2025 -
 The world of Divine Comedy, as shown by Michelangelo Caetani, duca02 abril 2025
The world of Divine Comedy, as shown by Michelangelo Caetani, duca02 abril 2025 -
 The Queen's Gambit' creators dismiss plans for a second season02 abril 2025
The Queen's Gambit' creators dismiss plans for a second season02 abril 2025 -
 qual melhor jogo de aposta para ganhar dinheiro,qual melhor jogo02 abril 2025
qual melhor jogo de aposta para ganhar dinheiro,qual melhor jogo02 abril 2025 -
 Nvidia GeForce RTX 4080 Founders Edition Review02 abril 2025
Nvidia GeForce RTX 4080 Founders Edition Review02 abril 2025 -
 Review - NieR Replicant ver.1.22474487139 - WayTooManyGames02 abril 2025
Review - NieR Replicant ver.1.22474487139 - WayTooManyGames02 abril 2025
