Malware analysis Malicious activity
Por um escritor misterioso
Last updated 05 abril 2025

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware analysis metasploit.bat Malicious activity

Feature Extraction and Detection of Malwares Using Machine Learning

Malware analysis index.html Malicious activity

Malware analysis CQChallenge5.zip Malicious activity

MetaDefender Cloud Advanced threat prevention and detection

Malware analysis cd53fba6ddd4ae4ef7a5747c6003236c85791477854cc1b7ce00e0f8ee7677d9 Malicious activity

StopRansomware: Rhysida Ransomware

Remediation and Malware Detection Overview

Malware analysis tt.7z Malicious activity

Top 10 Types of Information Security Threats for IT Teams

What is Malware? Definition, Types, Prevention - TechTarget
Lab 6-1 Solutions - Practical Malware Analysis [Book]
Recomendado para você
-
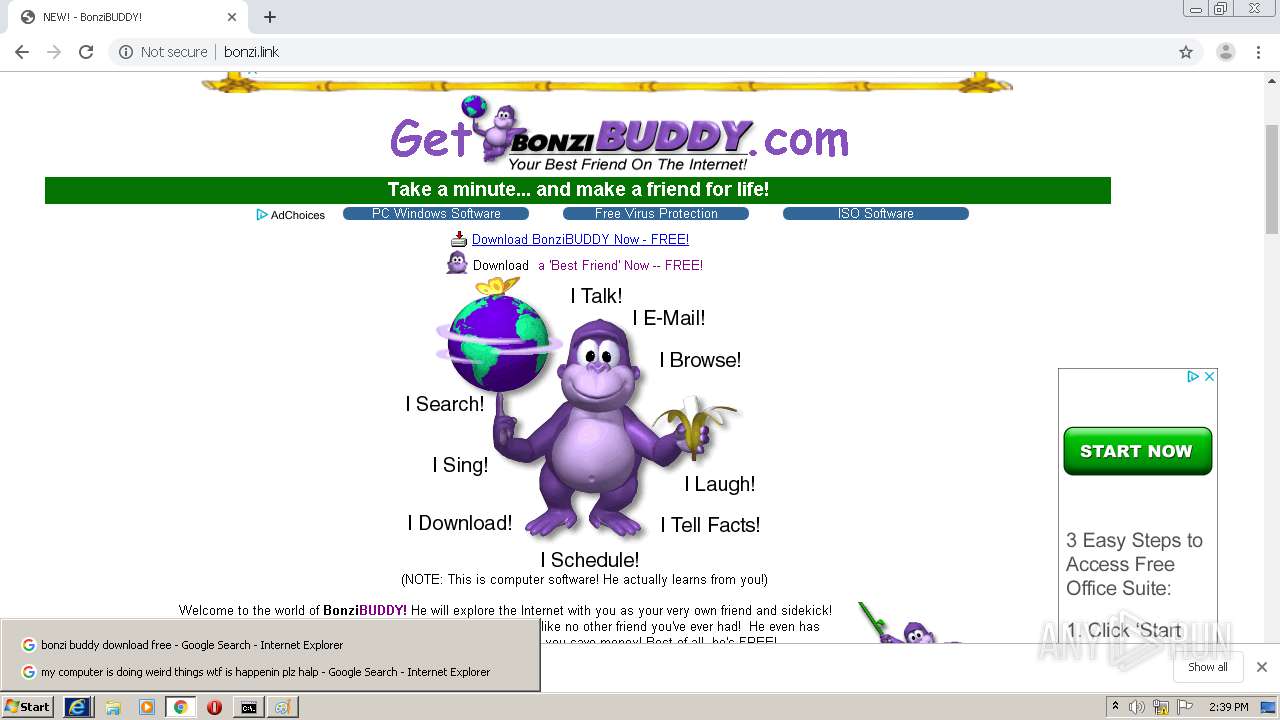
 BonziBuddy - Wikipedia05 abril 2025
BonziBuddy - Wikipedia05 abril 2025 -
 Bonzi Buddy, The SMG4/GLITCH Wiki05 abril 2025
Bonzi Buddy, The SMG4/GLITCH Wiki05 abril 2025 -
 BonziBUDDY gets a Virus BonziBUDDY Episode #4105 abril 2025
BonziBUDDY gets a Virus BonziBUDDY Episode #4105 abril 2025 -
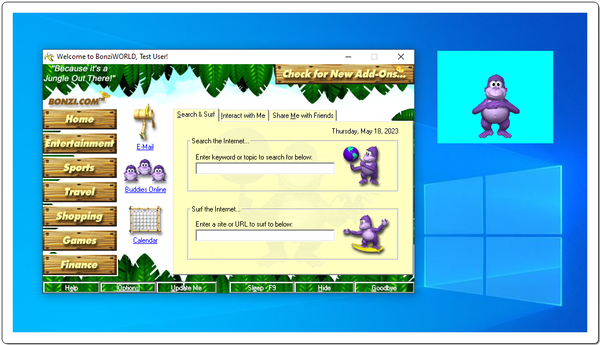 Weird Internet Things: What is Bonzi Buddy? - jv16 PowerTools Blog05 abril 2025
Weird Internet Things: What is Bonzi Buddy? - jv16 PowerTools Blog05 abril 2025 -
 Bonzie Buddy Get File - Colaboratory05 abril 2025
Bonzie Buddy Get File - Colaboratory05 abril 2025 -
 BonziBuddy (Shimeji-ee) : BonziBuddy : Free Download, Borrow, and Streaming : Internet Archive05 abril 2025
BonziBuddy (Shimeji-ee) : BonziBuddy : Free Download, Borrow, and Streaming : Internet Archive05 abril 2025 -
![Artwork Design] FREE Animated Bonzi Buddy Windows by joaomolfer on DeviantArt](https://images-wixmp-ed30a86b8c4ca887773594c2.wixmp.com/f/a9c946d7-463f-405c-b788-e3d37859efad/dg0dahn-33d1e61f-8508-4dbb-8506-28054ca93fc7.gif/v1/fill/w_1190,h_671,q_85,strp/_artwork_design__free_animated_bonzi_buddy_windows_by_joaomolfer_dg0dahn-pre.jpg?token=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJzdWIiOiJ1cm46YXBwOjdlMGQxODg5ODIyNjQzNzNhNWYwZDQxNWVhMGQyNmUwIiwiaXNzIjoidXJuOmFwcDo3ZTBkMTg4OTgyMjY0MzczYTVmMGQ0MTVlYTBkMjZlMCIsIm9iaiI6W1t7ImhlaWdodCI6Ijw9ODYyIiwicGF0aCI6IlwvZlwvYTljOTQ2ZDctNDYzZi00MDVjLWI3ODgtZTNkMzc4NTllZmFkXC9kZzBkYWhuLTMzZDFlNjFmLTg1MDgtNGRiYi04NTA2LTI4MDU0Y2E5M2ZjNy5naWYiLCJ3aWR0aCI6Ijw9MTUyOCJ9XV0sImF1ZCI6WyJ1cm46c2VydmljZTppbWFnZS5vcGVyYXRpb25zIl19.s41GswK-78o9G2NpUhZ00GdqxaIWd09wIDeRHQr8TZc) Artwork Design] FREE Animated Bonzi Buddy Windows by joaomolfer on DeviantArt05 abril 2025
Artwork Design] FREE Animated Bonzi Buddy Windows by joaomolfer on DeviantArt05 abril 2025 -
 MaxALERT Installer by Bonzi Software. : BONZI Software : Free Download, Borrow, and Streaming : Internet Archive05 abril 2025
MaxALERT Installer by Bonzi Software. : BONZI Software : Free Download, Borrow, and Streaming : Internet Archive05 abril 2025 -
MEMZ VS. Bonzi Buddy - video Dailymotion05 abril 2025
-
 Caillou downloads Bonzi Buddy on the school's computer/ Suspended05 abril 2025
Caillou downloads Bonzi Buddy on the school's computer/ Suspended05 abril 2025
você pode gostar
-
 Katekyō Hitman Reborn! - Japan Ryan05 abril 2025
Katekyō Hitman Reborn! - Japan Ryan05 abril 2025 -
 Hero (Dragon Quest), Dragon Quest Wiki05 abril 2025
Hero (Dragon Quest), Dragon Quest Wiki05 abril 2025 -
/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2021/z/3/eS2BV4TtqU410hHstdIQ/2015-07-29-jogos-gratis-plus-agosto-2015.jpg) God of War, Limbo e Lara Croft são jogos grátis da PS Plus em agosto05 abril 2025
God of War, Limbo e Lara Croft são jogos grátis da PS Plus em agosto05 abril 2025 -
 Pokemon Among Us Drip 205 abril 2025
Pokemon Among Us Drip 205 abril 2025 -
 Beautiful pixel art of a cyberpunk coffeeshop in the rain05 abril 2025
Beautiful pixel art of a cyberpunk coffeeshop in the rain05 abril 2025 -
Motosserra Anime Homem Makima Quanxi Denji Power Mitaka Asa Reze Angel Devil Hayakawa Aki Yoshida Hirofumi Pochita Boneca De Pelúcia Desenho Animado Macio Brinquedo Recheado Presente De Natal Infantil - Corre Que05 abril 2025
-
 Stream Truck Simulator Ultimate: O melhor jogo de caminhão com mod05 abril 2025
Stream Truck Simulator Ultimate: O melhor jogo de caminhão com mod05 abril 2025 -
 9 Satra - A Lenda do Muay Thai - Filme Completo Dublado - Animação, Cine Animado em 202305 abril 2025
9 Satra - A Lenda do Muay Thai - Filme Completo Dublado - Animação, Cine Animado em 202305 abril 2025 -
 Livro Barbie - 365 Desenhos Para Colorir Crianças Filhos Infantil Desenho Ciranda Brincar Pintar Colorir Passatempos - Livro de Colorir - Magazine Luiza05 abril 2025
Livro Barbie - 365 Desenhos Para Colorir Crianças Filhos Infantil Desenho Ciranda Brincar Pintar Colorir Passatempos - Livro de Colorir - Magazine Luiza05 abril 2025 -
 How To Evolve Units in Roblox Anime Adventures05 abril 2025
How To Evolve Units in Roblox Anime Adventures05 abril 2025