Malware analysis Malicious activity
Por um escritor misterioso
Last updated 15 abril 2025

Dynamic malware analysis [34]

Feature Extraction and Detection of Malwares Using Machine

Remediation and Malware Detection Overview

Malware Analysis Benefits Incident Response

Top 10 Types of Information Security Threats for IT Teams

PROUD-MAL: static analysis-based progressive framework for deep
Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware: 9781788392501: A,

Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware

Routers Roasting on an Open Firewall: the KV-botnet Investigation

What is Malware? Definition, Types, Prevention - TechTarget

What Is Malware Analysis? Definition, Types, Stages, and Best

Malware Analysis: Steps & Examples - CrowdStrike
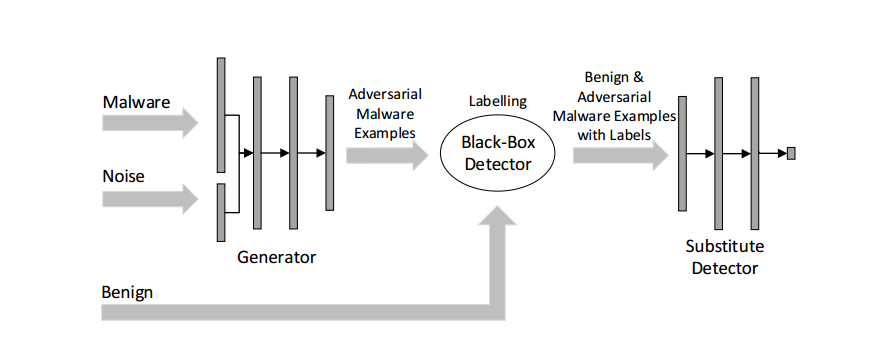
Malware Detection

StopRansomware: Rhysida Ransomware
Recomendado para você
-
 Pokémon Vortex - Bulbapedia, the community-driven Pokémon encyclopedia15 abril 2025
Pokémon Vortex - Bulbapedia, the community-driven Pokémon encyclopedia15 abril 2025 -
 John Shedletsky on X: Back when I was the gfx artist for 2012. Those play buttons are oof. / X15 abril 2025
John Shedletsky on X: Back when I was the gfx artist for 2012. Those play buttons are oof. / X15 abril 2025 -
 Pokemon Vortex v3 Spin Bot v215 abril 2025
Pokemon Vortex v3 Spin Bot v215 abril 2025 -
 Pokemon vortex 2017 Hack Legendary Shiny 100% Working!!15 abril 2025
Pokemon vortex 2017 Hack Legendary Shiny 100% Working!!15 abril 2025 -
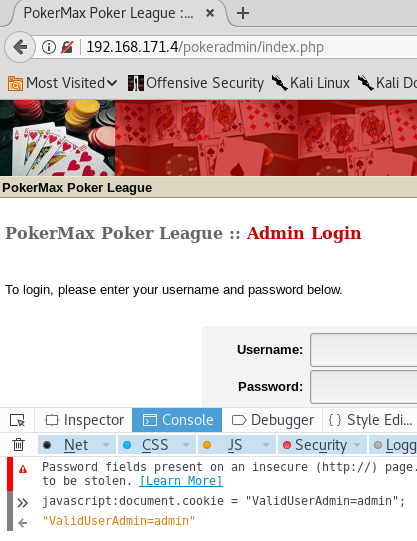 Casino Royale VulnHub Walkthrough - Bond, James Bond15 abril 2025
Casino Royale VulnHub Walkthrough - Bond, James Bond15 abril 2025 -
 Pokemon Vortex V3 Game Free Download - Colaboratory15 abril 2025
Pokemon Vortex V3 Game Free Download - Colaboratory15 abril 2025 -
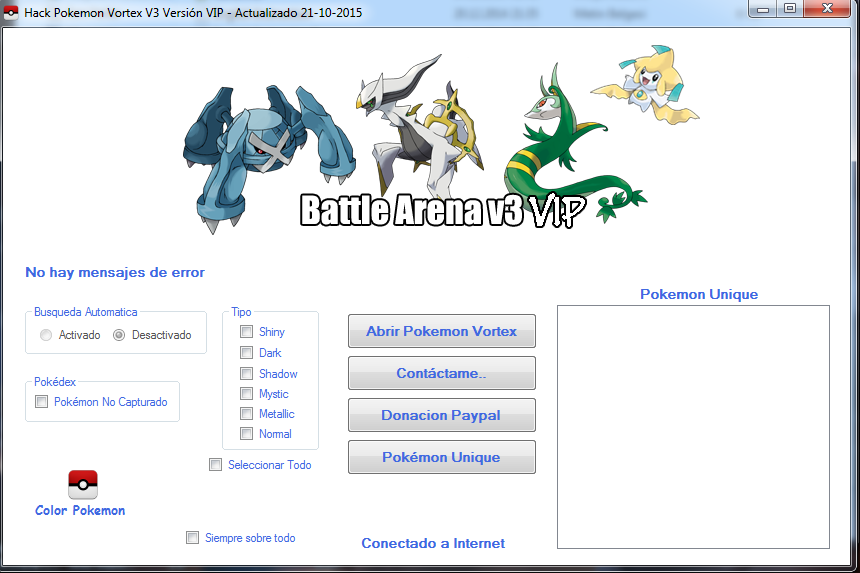 pokemon vortex v3 vip hack ve vip bot15 abril 2025
pokemon vortex v3 vip hack ve vip bot15 abril 2025 -
 A Gloomy Outlook At the NSS Blog - NASA Watch15 abril 2025
A Gloomy Outlook At the NSS Blog - NASA Watch15 abril 2025 -
 Computer Face (Remix) - Flying Lotus15 abril 2025
Computer Face (Remix) - Flying Lotus15 abril 2025 -
 MSI Vortex Mini Gaming PC Now on Sale15 abril 2025
MSI Vortex Mini Gaming PC Now on Sale15 abril 2025
você pode gostar
-
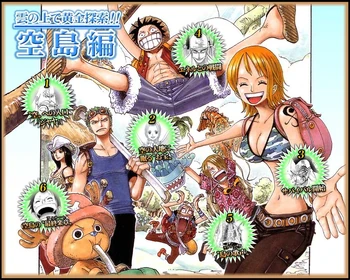 Sky Island Saga One Piece+BreezeWiki15 abril 2025
Sky Island Saga One Piece+BreezeWiki15 abril 2025 -
 playmobil sombrero gorro sheriff vaquero oeste - Buy Playmobil on todocoleccion15 abril 2025
playmobil sombrero gorro sheriff vaquero oeste - Buy Playmobil on todocoleccion15 abril 2025 -
 Painel Tecido Redondo 1.30M Moana Baby Decoração 03 em Promoção na Americanas15 abril 2025
Painel Tecido Redondo 1.30M Moana Baby Decoração 03 em Promoção na Americanas15 abril 2025 -
 Ivar the Boneless by MakaIlustracion on DeviantArt15 abril 2025
Ivar the Boneless by MakaIlustracion on DeviantArt15 abril 2025 -
 ALAN BECKER NEW VIDEO SNEAK PEAK?!!? : r/AlanBecker15 abril 2025
ALAN BECKER NEW VIDEO SNEAK PEAK?!!? : r/AlanBecker15 abril 2025 -
 Kaiko sareta Ankoku Heishi (30-dai) no Slow na Second Life Manga Chapter 1.215 abril 2025
Kaiko sareta Ankoku Heishi (30-dai) no Slow na Second Life Manga Chapter 1.215 abril 2025 -
MAME) Street Fighter 2 - 03 - Blanka - video Dailymotion15 abril 2025
-
 Category:Tales of Zestiria Characters, Talespedia15 abril 2025
Category:Tales of Zestiria Characters, Talespedia15 abril 2025 -
 Serval - News - IMDb15 abril 2025
Serval - News - IMDb15 abril 2025 -
 Colorful dream catcher icon cartoon style Vector Image15 abril 2025
Colorful dream catcher icon cartoon style Vector Image15 abril 2025