How Do MAC Spoofing Attacks Work?
Por um escritor misterioso
Last updated 05 abril 2025

In this blog, we will go into the complexities of MAC spoofing, analyzing its repercussions and emphasizing the importance of having strong security policies in place.
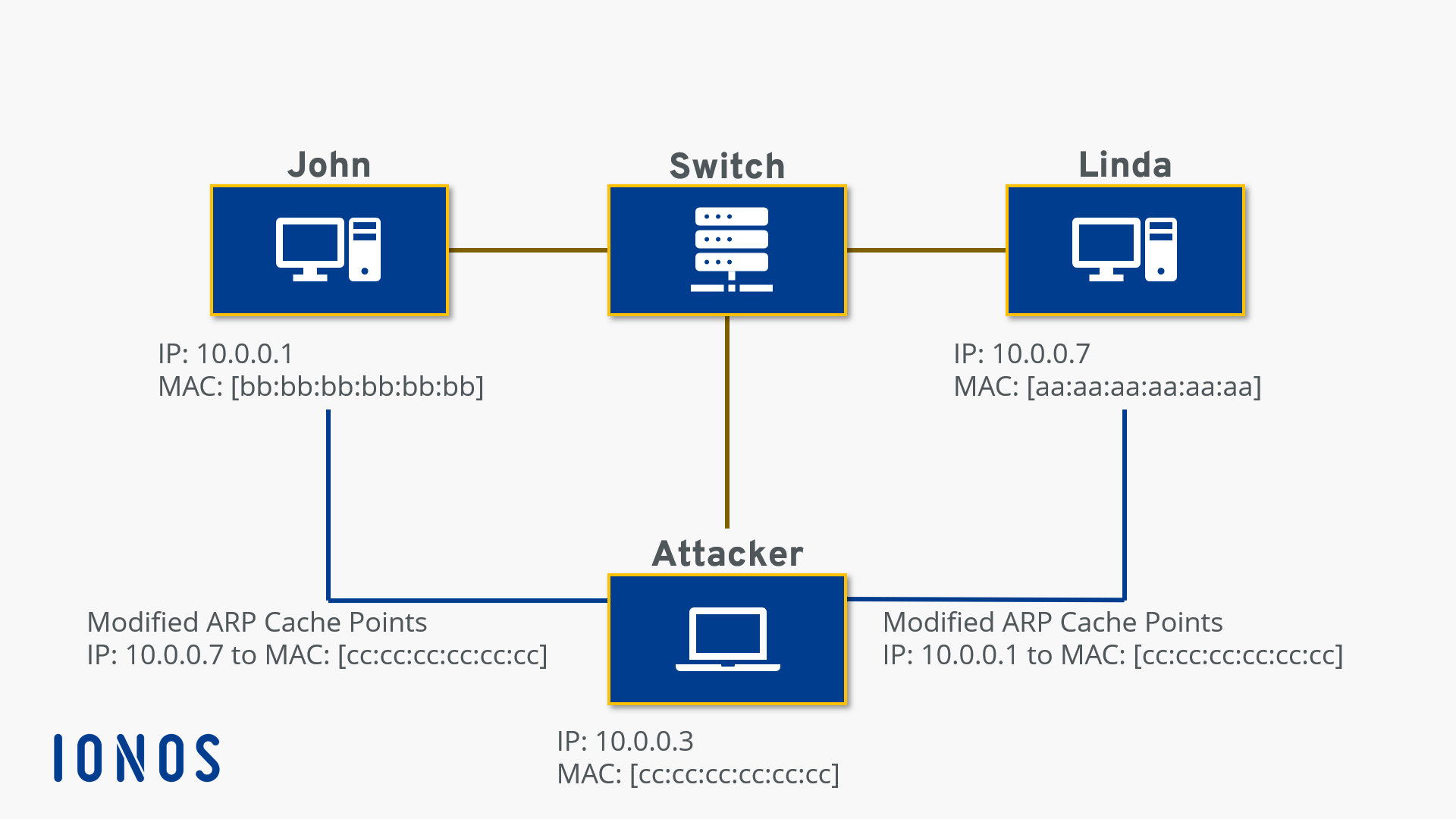
What is ARP Spoofing and how does it work? - IONOS CA
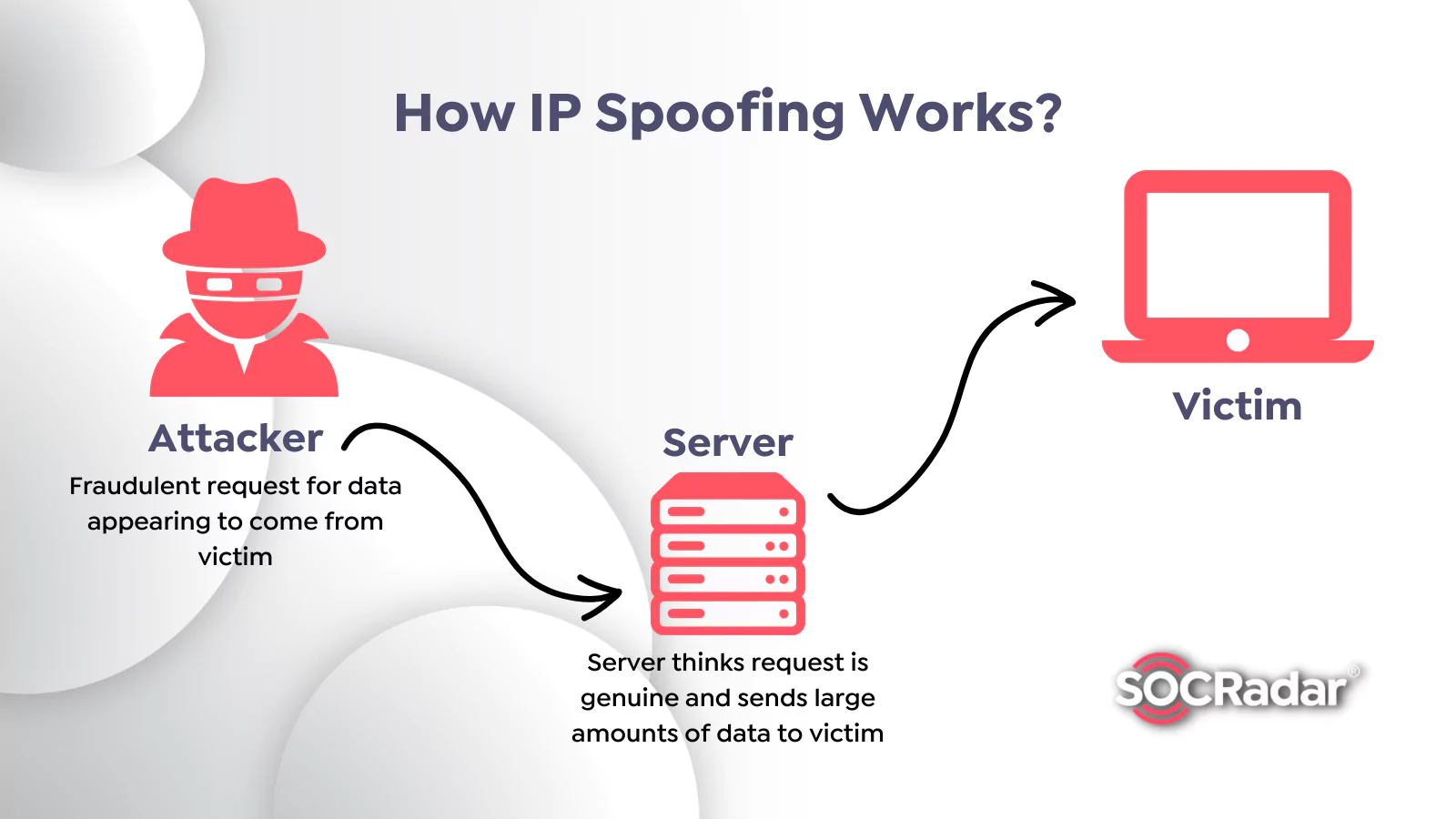
What is Spoofing Attack and How to Prevent It? - SOCRadar® Cyber Intelligence Inc.
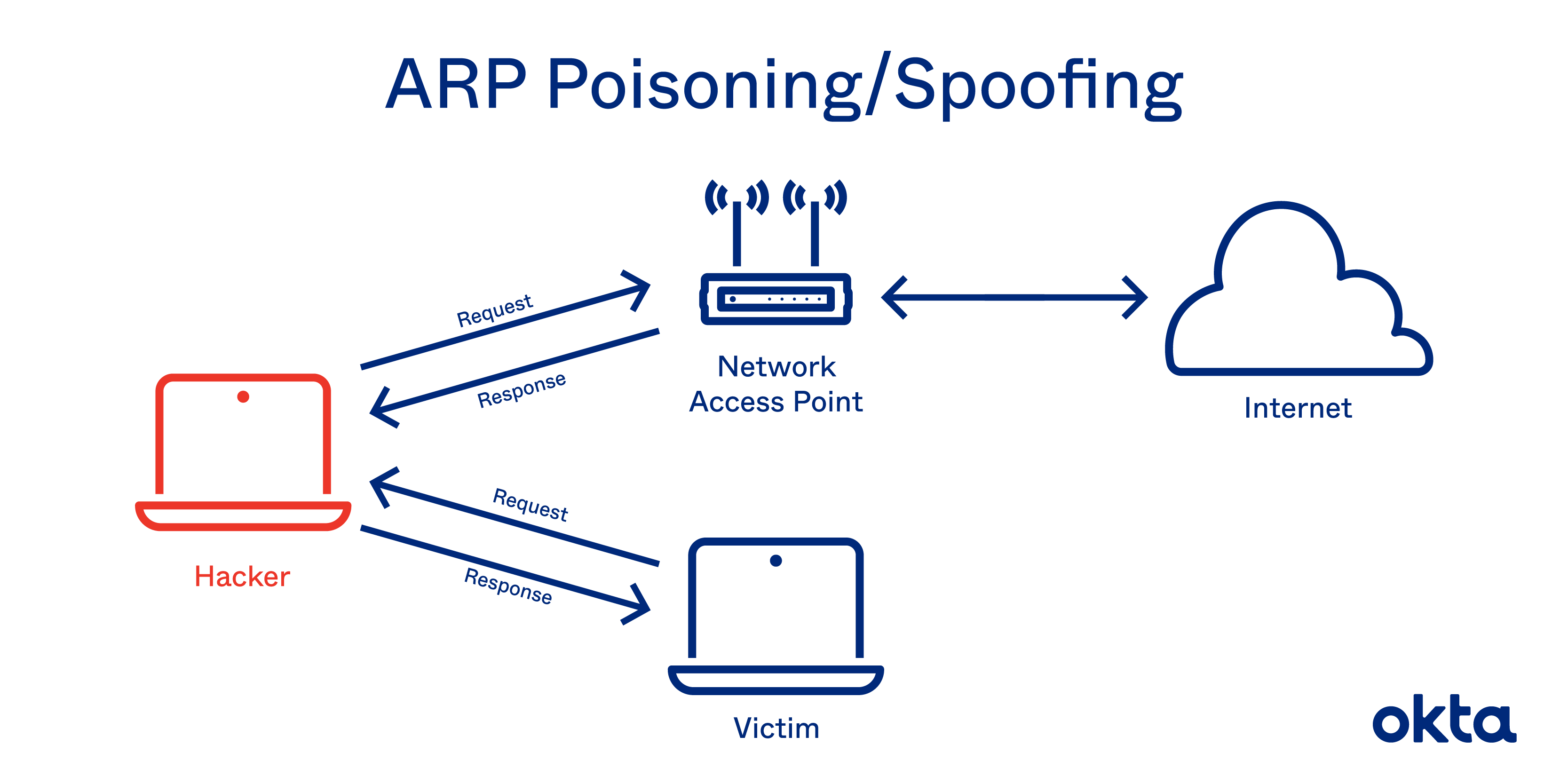
ARP Poisoning: Definition, Techniques, Defense & Prevention

Understanding MAC Spoofing Attacks
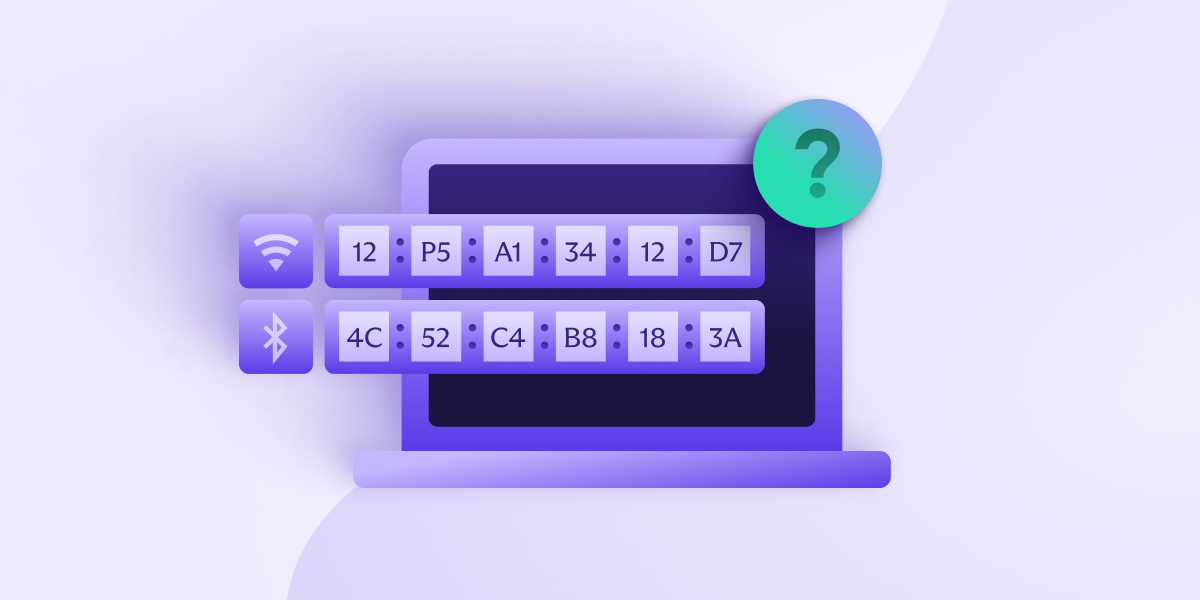
What is a MAC address, and what can it reveal about you?

Configuring MAC-IP Anti-Spoof

What is IP Spoofing?
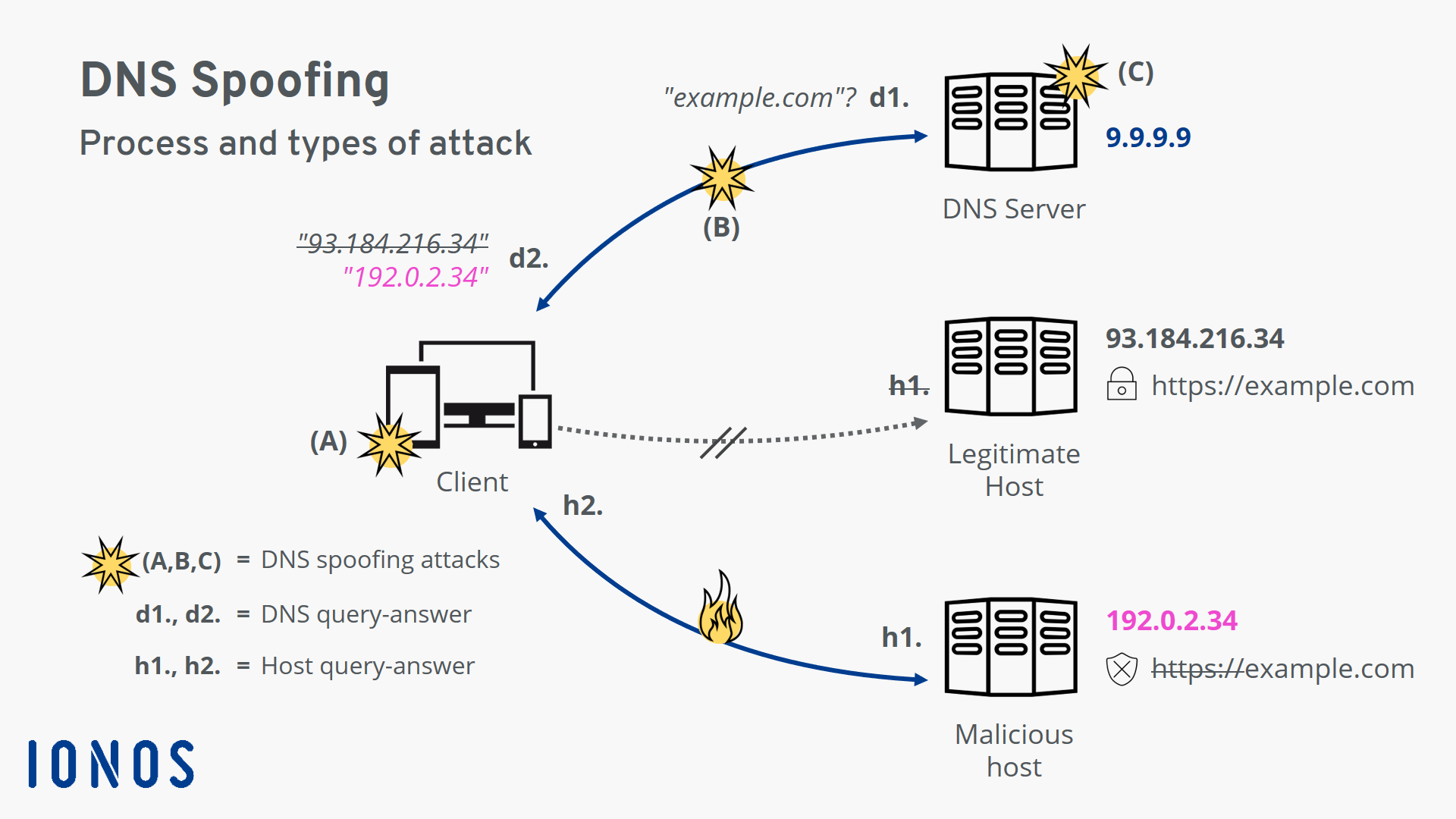
DNS spoofing Definition, explanation, and protection measures - IONOS
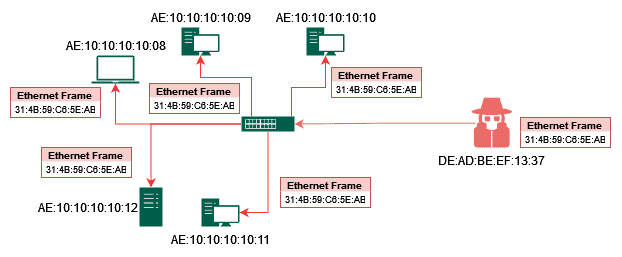
How MAC Flooding and Cloning Attacks Work?
Recomendado para você
-
Bbc android iplayer download05 abril 2025
-
 Redengine Lifetime - Melhor Modmenu Para Fivem - Gta - DFG05 abril 2025
Redengine Lifetime - Melhor Modmenu Para Fivem - Gta - DFG05 abril 2025 -
 HOW TO REDEEM YOUR REDENGINE KEY AND DOWNLOAD REDENGINE!05 abril 2025
HOW TO REDEEM YOUR REDENGINE KEY AND DOWNLOAD REDENGINE!05 abril 2025 -
 A comprehensive survey on radio frequency (RF) fingerprinting05 abril 2025
A comprehensive survey on radio frequency (RF) fingerprinting05 abril 2025 -
 Visitor's Guide University of Arkansas05 abril 2025
Visitor's Guide University of Arkansas05 abril 2025 -
 Engineering Proceedings, Free Full-Text05 abril 2025
Engineering Proceedings, Free Full-Text05 abril 2025 -
 Who Killed Art Deco?: A Novel - Kindle edition by Barris, Chuck05 abril 2025
Who Killed Art Deco?: A Novel - Kindle edition by Barris, Chuck05 abril 2025 -
 Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's05 abril 2025
Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's05 abril 2025 -
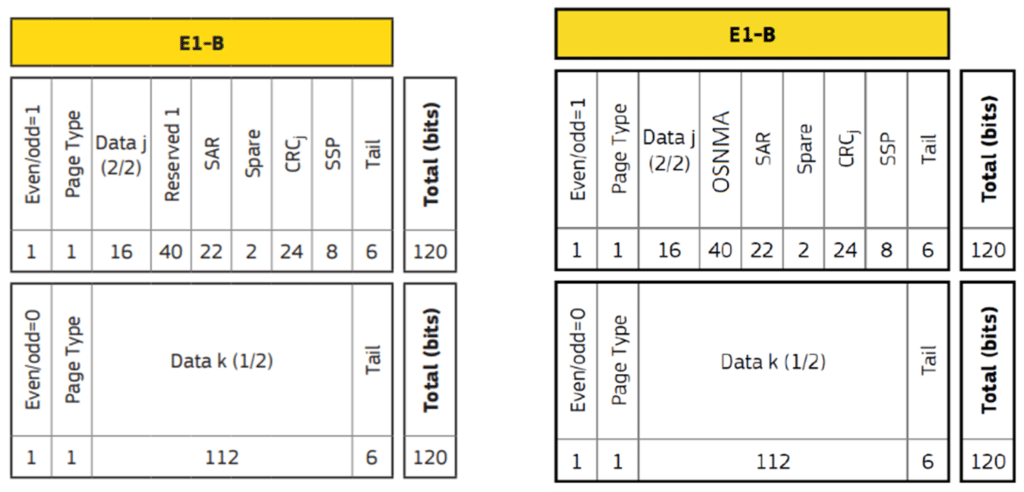 Testing a Receiver's Galileo OS-NMA Capability Using Skydel - Safran - Navigation & Timing05 abril 2025
Testing a Receiver's Galileo OS-NMA Capability Using Skydel - Safran - Navigation & Timing05 abril 2025 -
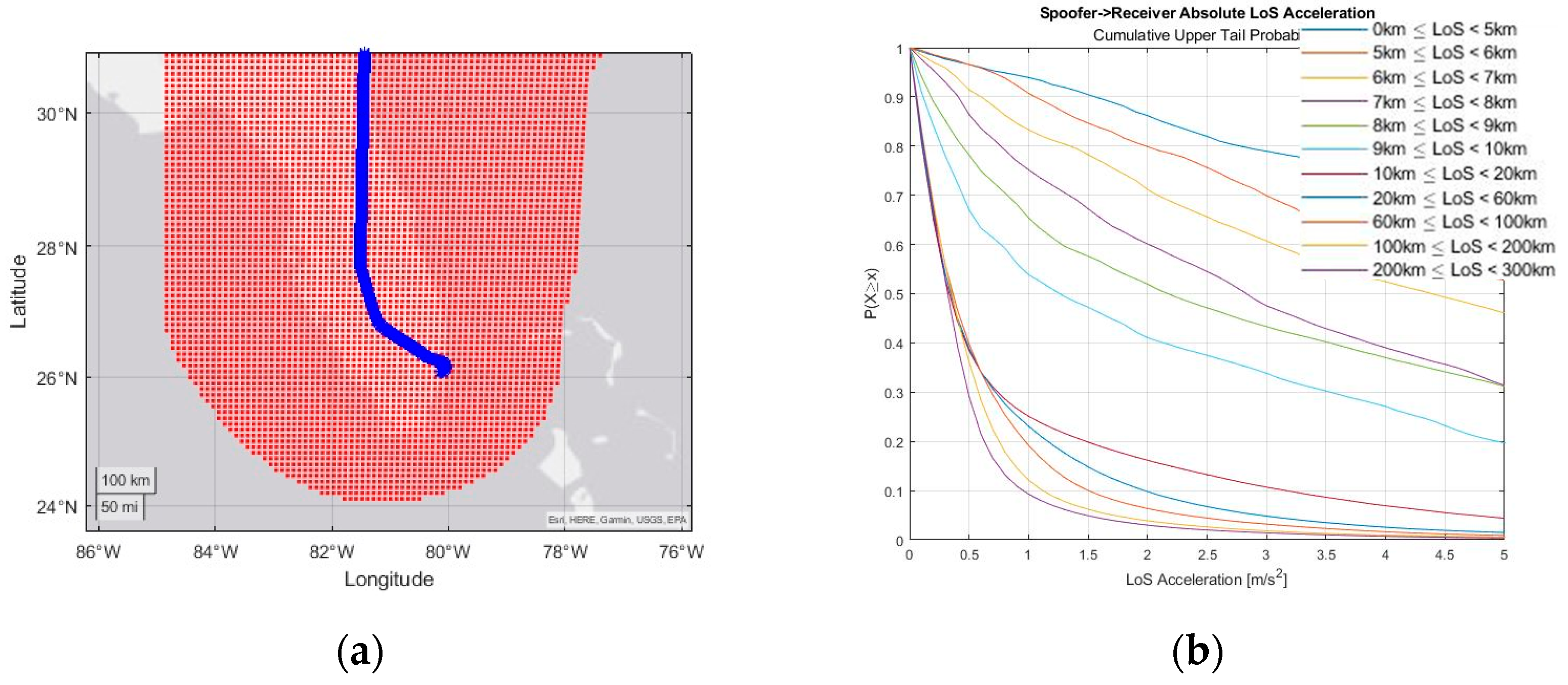
 DeepPOSE: Detecting GPS spoofing attack via deep recurrent neural network - ScienceDirect05 abril 2025
DeepPOSE: Detecting GPS spoofing attack via deep recurrent neural network - ScienceDirect05 abril 2025
você pode gostar
-
 File talk:Ultimate Custom Night, Scott Cawthon Wiki05 abril 2025
File talk:Ultimate Custom Night, Scott Cawthon Wiki05 abril 2025 -
Mewtwo returns and is out for revenge! Will Ash and his friends be able to stop Mewtwo's path of destruction? Revisit this CGI…05 abril 2025
-
Melhores Jogos para DAR GRAU De Moto para CELULAR📲🎮 (L!NK NA MINHA B05 abril 2025
-
 Alive and Kicking05 abril 2025
Alive and Kicking05 abril 2025 -
 One Piece Figure - Roronoa Zoro Monkey D Luffy Boa Hancock Mini Action Figure 8cm05 abril 2025
One Piece Figure - Roronoa Zoro Monkey D Luffy Boa Hancock Mini Action Figure 8cm05 abril 2025 -
 The Cuphead Show! premieres February 18, official trailer - Gematsu05 abril 2025
The Cuphead Show! premieres February 18, official trailer - Gematsu05 abril 2025 -
Isekai Nonbiri Nouka - 01 PDF, PDF, Plough05 abril 2025
-
 2016 Summer Paralympics - Wikipedia05 abril 2025
2016 Summer Paralympics - Wikipedia05 abril 2025 -
 Download and Play Hill Climb Racing 2 on PC & Mac (Emulator)05 abril 2025
Download and Play Hill Climb Racing 2 on PC & Mac (Emulator)05 abril 2025 -
 FNF rap battle on Friday night android iOS apk download for free05 abril 2025
FNF rap battle on Friday night android iOS apk download for free05 abril 2025


