Credential Stuffing 2.0: The Use of Proxies, CAPTCHA Bypassing
Por um escritor misterioso
Last updated 12 abril 2025
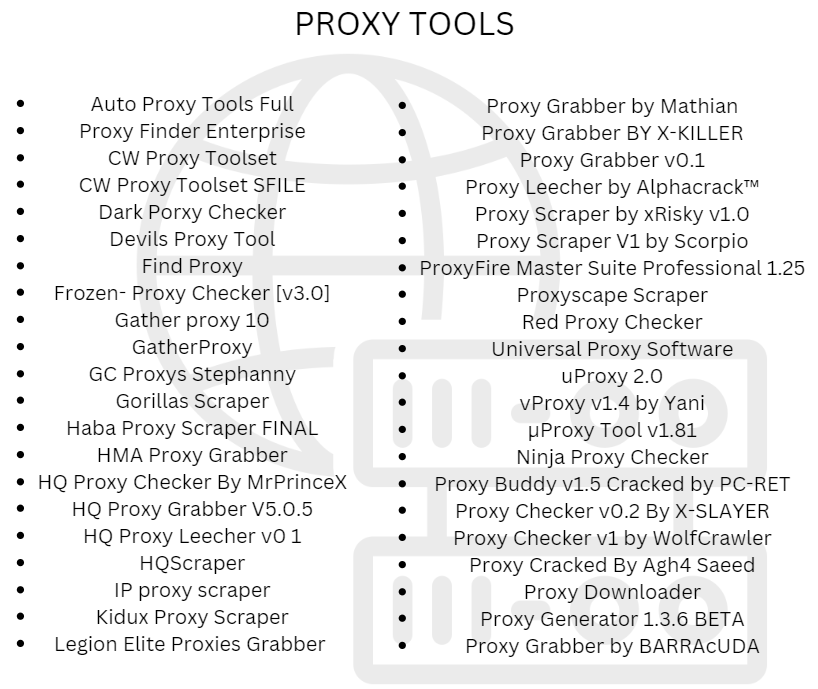
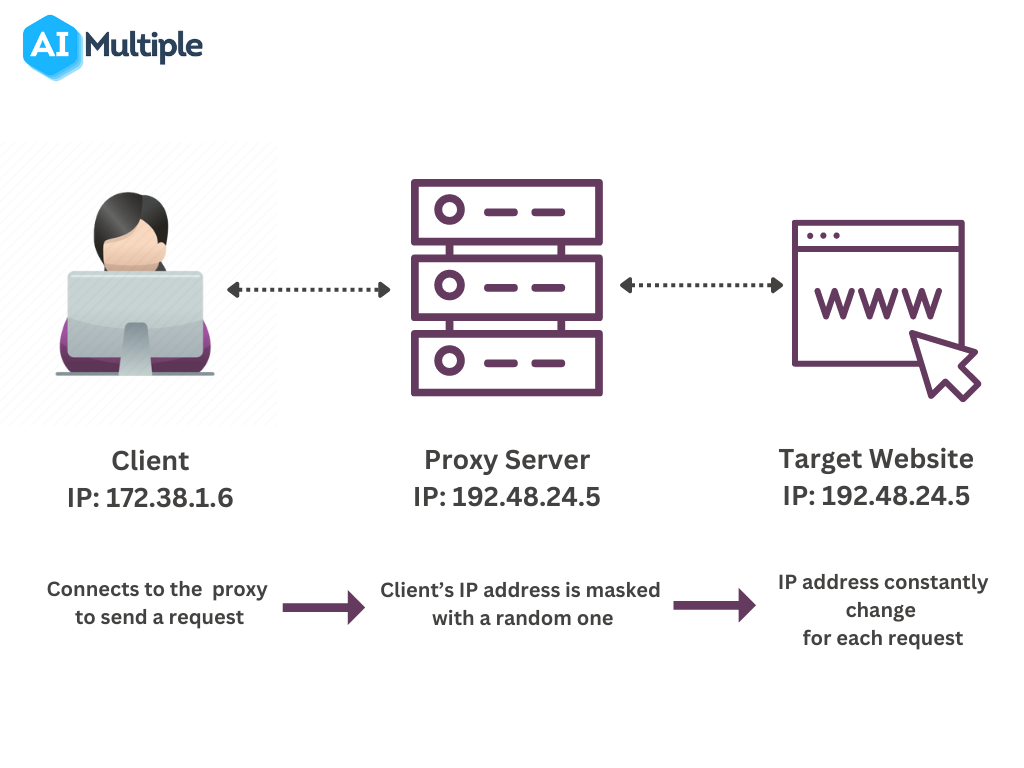
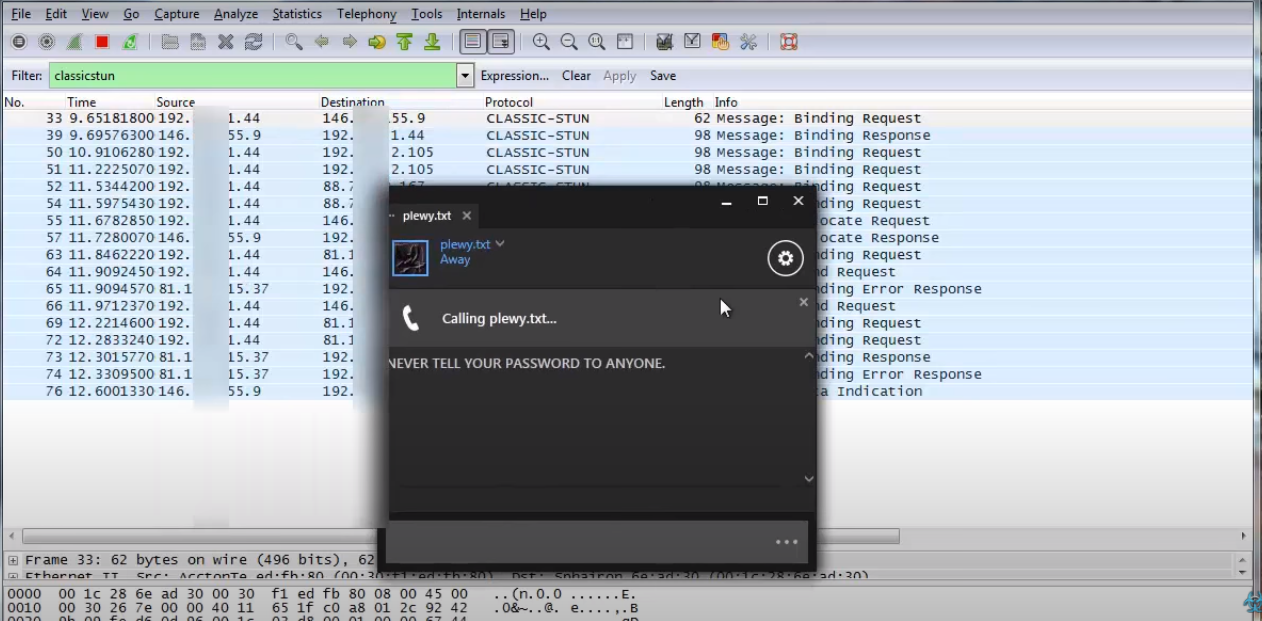
Welcome to the new age of cyber attacks, where hackers have taken credential stuffing to the next level. Meet Credential Stuffing 2.0, where the use of proxies, CAPTCHA bypassing, CloudFlare security, and GUI tools have become the norm..

Email Compromise with Credential Stuffing Attack Tools

The Anatomy of Highly Profitable Credential Stuffing Attacks
The State of Credential Stuffing and the Future of Account Takeovers.
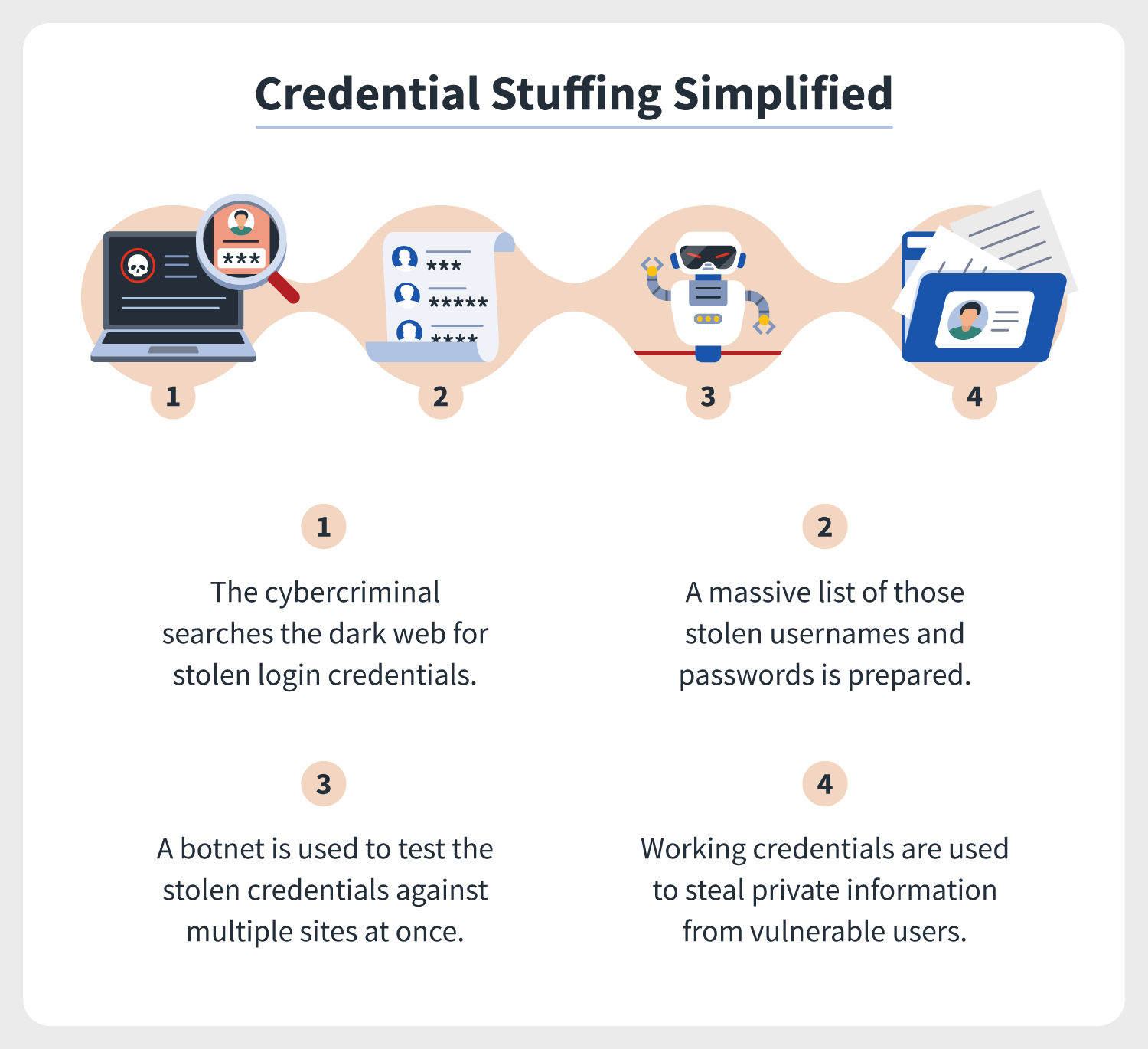
Credential stuffing simplified + attack protection tips
How to Bypass DataDome: Complete Guide 2023 - ZenRows
Best CAPTCHA Proxies in 2023 - ZenRows
The Ultimate Guide to Avoiding CAPTCHAs in Web Scraping

The credential stuffing bots are back, and still not playing fair
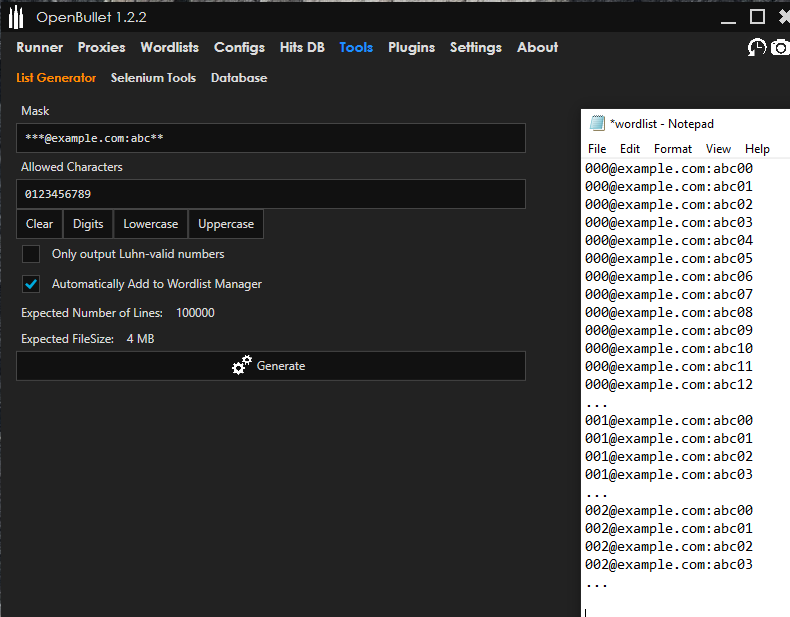
How Cybercriminals Abuse OpenBullet for Credential Stuffing

10 Tips To Stop Credential Stuffing Attacks, by Jarrod Overson

Email Compromise with Credential Stuffing Attack Tools
Recomendado para você
-
 How to Get Someones IP from Steam Id12 abril 2025
How to Get Someones IP from Steam Id12 abril 2025 -
 IP Address Scanner - IP Scanner (FREE TRIAL)12 abril 2025
IP Address Scanner - IP Scanner (FREE TRIAL)12 abril 2025 -
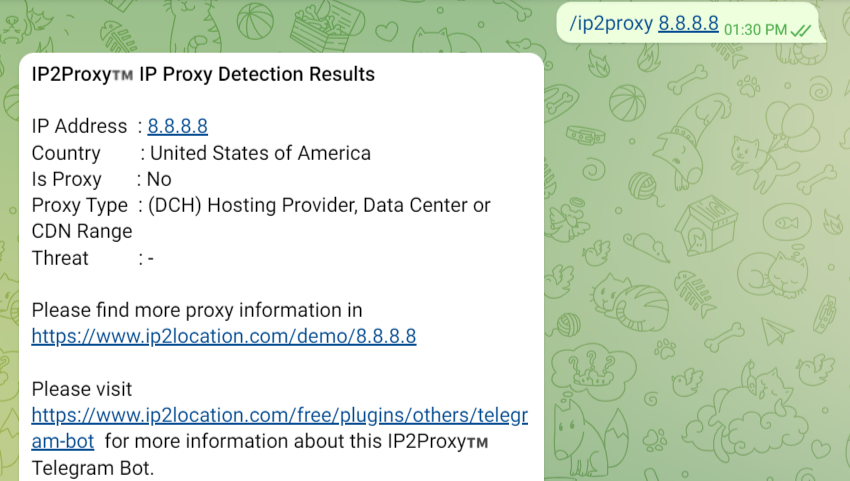 Telegram bot for IP Geolocation12 abril 2025
Telegram bot for IP Geolocation12 abril 2025 -
 3 Ways to Get Someone's IP Address12 abril 2025
3 Ways to Get Someone's IP Address12 abril 2025 -
image-logger · GitHub Topics · GitHub12 abril 2025
-
 MAC Scanner, Free MAC Address Scanner - Colasoft12 abril 2025
MAC Scanner, Free MAC Address Scanner - Colasoft12 abril 2025 -
 Ip Location Plugins, Code & Scripts12 abril 2025
Ip Location Plugins, Code & Scripts12 abril 2025 -
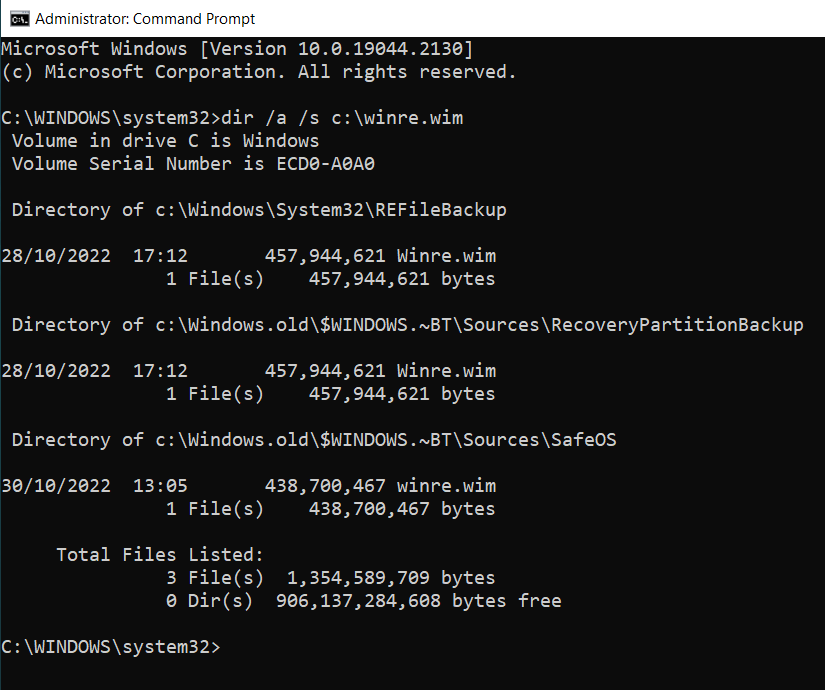
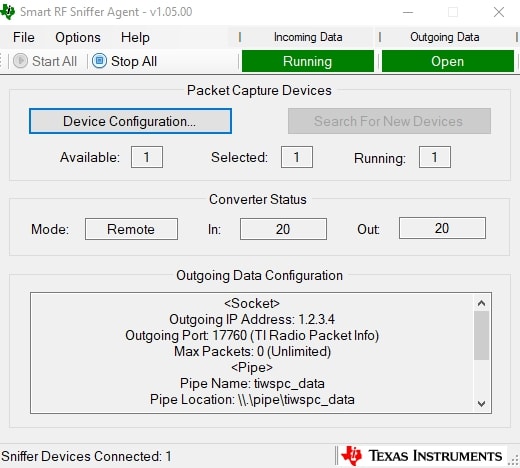 PACKET-SNIFFER Calculation tool12 abril 2025
PACKET-SNIFFER Calculation tool12 abril 2025 -
 IP Checker12 abril 2025
IP Checker12 abril 2025 -
 Discord IP Resolver How to Pull IP on Discord? [2023 Update12 abril 2025
Discord IP Resolver How to Pull IP on Discord? [2023 Update12 abril 2025
você pode gostar
-
 EA Says Please Don't Rage Quit FIFA 22 After Banning 30K+ Players12 abril 2025
EA Says Please Don't Rage Quit FIFA 22 After Banning 30K+ Players12 abril 2025 -
 Marvel Reveals New Release Date for Loki Disney+ Show12 abril 2025
Marvel Reveals New Release Date for Loki Disney+ Show12 abril 2025 -
 Do you have windows 11? • page 1/3 • Off-Topic Discussion •12 abril 2025
Do you have windows 11? • page 1/3 • Off-Topic Discussion •12 abril 2025 -
 O FILME DO MARIO AZEDOU NAS CRÍTICAS12 abril 2025
O FILME DO MARIO AZEDOU NAS CRÍTICAS12 abril 2025 -
 2016 Chateau Grand Bertin de Saint Clair, Medoc, France12 abril 2025
2016 Chateau Grand Bertin de Saint Clair, Medoc, France12 abril 2025 -
Toradora is really popular, so why does the author create more12 abril 2025
-
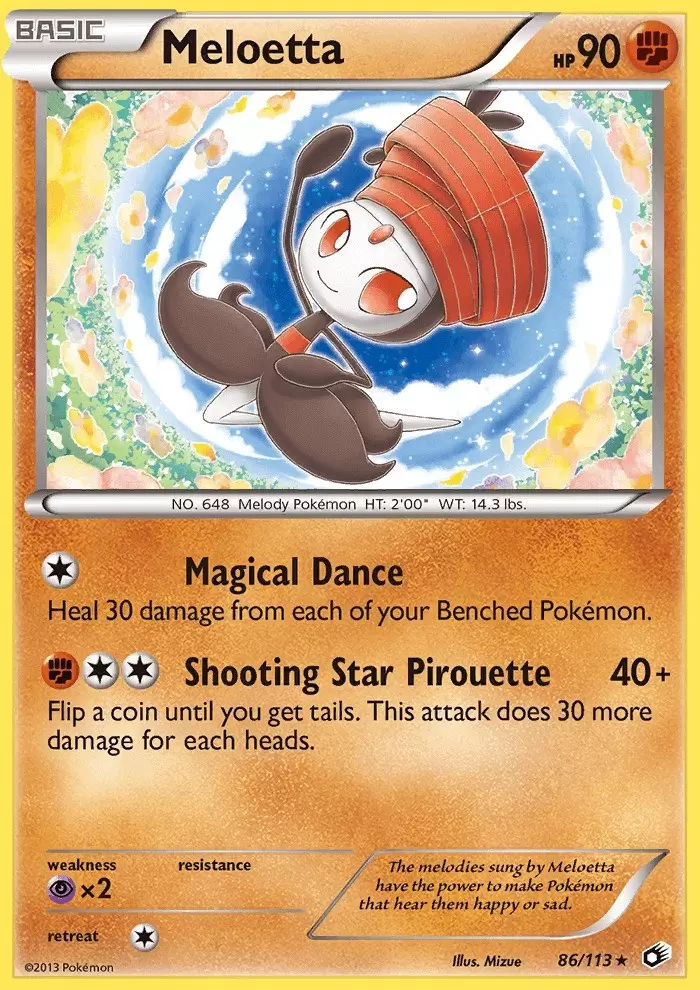 Meloetta - Legendary Treasures Pokémon card 86/11312 abril 2025
Meloetta - Legendary Treasures Pokémon card 86/11312 abril 2025 -
 Sobre uma roda da bicicleta, douradense compartilha desafios do grau nas redes sociais - Dourados News12 abril 2025
Sobre uma roda da bicicleta, douradense compartilha desafios do grau nas redes sociais - Dourados News12 abril 2025 -
 Barcelona, Part 1 - by Ada Hoffmann - Everything Is True12 abril 2025
Barcelona, Part 1 - by Ada Hoffmann - Everything Is True12 abril 2025 -
 Anime hottie GIFs - Find & Share on GIPHY12 abril 2025
Anime hottie GIFs - Find & Share on GIPHY12 abril 2025